This page has been machine-translated from the original page.
I participated in corCTF 2024, which started on July 27, 2024.
This time the Rev challenges were far too difficult for me, and I did not feel like I could solve any of them, so I retired early after solving only two Forensics problems.
I wrote brief writeups only for the challenges I solved, so I am collecting them here.
Table of Contents
the-conspiracy(Forensics)
Our intelligence team created a chat app, and secretly distributed it to the lemonthinker gang. We’ve given you the application source and a capture taken by one of our agents - can you uncover their plans?
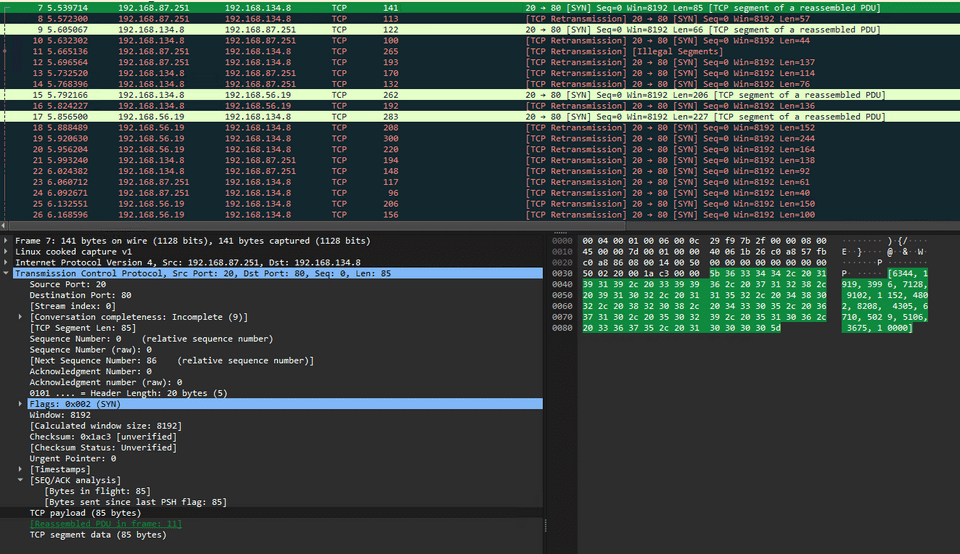
Analyzing the pcap file provided with the challenge shows that meaningless-looking payloads were being sent and received as shown below.
After checking the script that was also provided with the challenge, I confirmed that the keys and messages encrypted by the encrypt function seemed to be exchanged as TCP packets.
import random
from scapy.all import *
import csv
sources, destinations, messages = [], [], []
with open('chatlogs.csv', mode='r') as file:
csv_reader = csv.reader(file)
for row in csv_reader:
sources.append(row[0])
destinations.append(row[1])
messages.append(row[2])
def encrypt(message):
messagenums = []
for character in message:
messagenums.append(ord(character))
keys = []
for i in range(len(messagenums)):
keys.append(random.randint(10, 100))
finalmessage = []
for i in range(len(messagenums)):
finalmessage.append(messagenums[i] * keys[i])
return keys, finalmessage
for i in range(len(messages)):
finalmessage, keys = encrypt(messages[i])
print(finalmessage, keys)
packet1 = IP(src=sources[i], dst=destinations[i])/TCP(dport=80)/Raw(load=str(finalmessage))
send(packet1)
packet2 = IP(src=sources[i], dst=destinations[i])/TCP(dport=80)/Raw(load=str(keys))
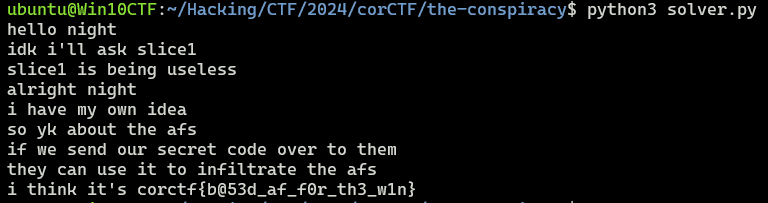
send(packet2)So I wrote the following script to decrypt each message and obtained the flag.
import ast
from scapy.all import *
def print_decrypted(p,k):
for i in range(len(p)):
print(chr(p[i]//k[i]), end="")
print()
return
def extract_tcp_payload(pcap_file, src_ip=None, dst_ip=None, src_port=None, dst_port=None):
packets = rdpcap(pcap_file)
payloads = []
for packet in packets:
if packet.haslayer('TCP'):
if src_ip and packet['IP'].src != src_ip:
continue
if dst_ip and packet['IP'].dst != dst_ip:
continue
# if src_port and packet['TCP'].sport != src_port:
# continue
if dst_port and packet['TCP'].dport != dst_port:
continue
tcp_payload = bytes(packet['TCP'].payload)
if tcp_payload:
payloads.append(tcp_payload)
return payloads
pcap_file = "challenge.pcap"
src_ip = "192.168.134.8"
dst_ip = "192.168.87.251"
src_port = 0
dst_port = 80
payloads = extract_tcp_payload(pcap_file, src_ip, dst_ip, src_port, dst_port)
for i, payload in enumerate(payloads):
if i % 2 == 0:
p = ast.literal_eval(payload.decode())
else:
k = ast.literal_eval(payload.decode())
print_decrypted(p,k)Being able to analyze pcap files with scapy was extremely convenient. It seems easier than using tcpdump.
infiltration(Forensic)
After successfully infiltrating the lemonthinker gang, we’ve obtained their current location - the UK. We’ve attained some security logs from a gang member’s PC, but need some help in answering information relating to these.
This challenge involved analyzing the Windows Security Event Log provided with the challenge and answering six questions.
Q1
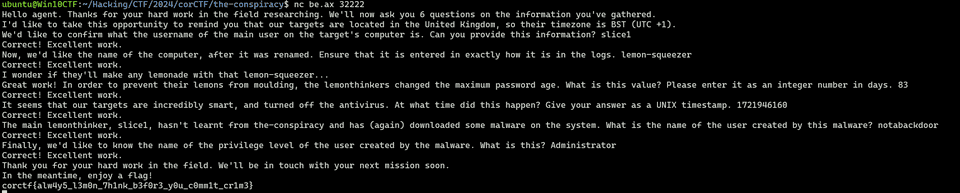
Hello agent. Thanks for your hard work in the field researching. We’ll now ask you 6 questions on the information you’ve gathered. I’d like to take this opportunity to remind you that our targets are located in the United Kingdom, so their timezone is BST (UTC +1). We’d like to confirm what the username of the main user on the target’s computer is. Can you provide this information?
The administrator user that was added first looked like the likely one, and slice1 was the correct answer.
Q2
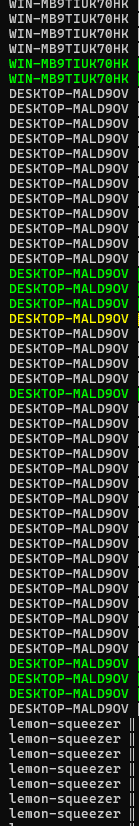
Now, we’d like the name of the computer, after it was renamed. Ensure that it is entered in exactly how it is in the logs.
The computer name was changed twice, and after the change made by what seemed to be the attacker, it was lemon-squeezer.
Q3
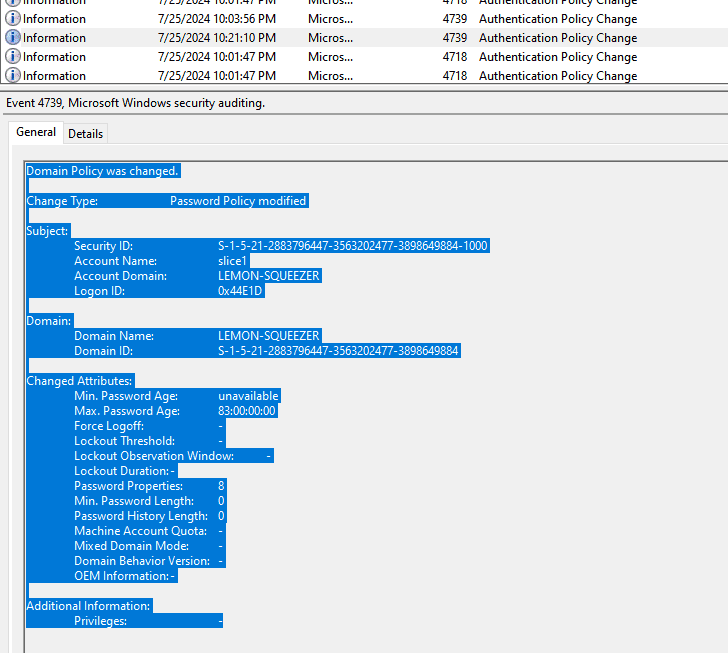
I wonder if they’ll make any lemonade with that lemon-squeezer… Great work! In order to prevent their lemons from moulding, the lemonthinkers changed the maximum password age. What is this value? Please enter it as an integer number in days.
From the password-policy change audit, you can tell that it was extended to 83 days.
Q4
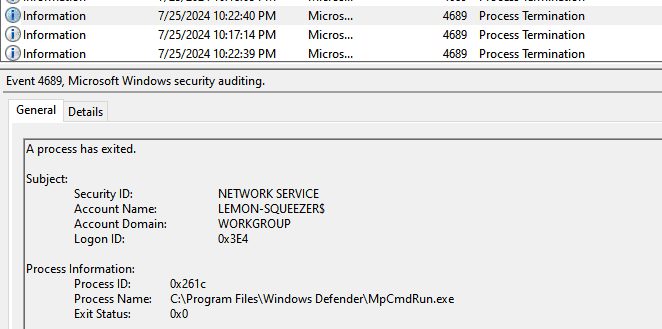
It seems that our targets are incredibly smart, and turned off the antivirus. At what time did this happen? Give your answer as a UNIX timestamp.
Converting the time when Defender was stopped into a UNIX timestamp gives 1721946160.
Q5
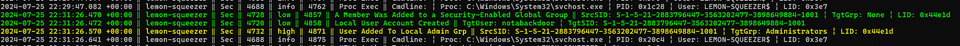
The main lemonthinker, slice1, hasn’t learnt from the-conspiracy and has (again) downloaded some malware on the system. What is the name of the user created by this malware?
The answer is the user notabackdoor, which was the last account created.
Q6
Finally, we’d like to know the name of the privilege level of the user created by the malware. What is this?
The answer here was simply Administrator.
The final answers were as follows.
slice1
lemon-squeezer
83
1721946160
notabackdoor
AdministratorSubmitting these answers gives the flag.
Analysis Notes
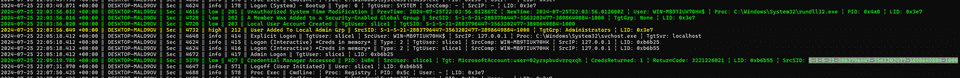
First, I analyzed the event log with Hayabusa.
.\hayabusa-2.5.1-win-x64.exe csv-timeline -d "C:\Users\kash1064\Downloads"At first, it looks like the user with SID S-1-5-21-2883796447-3563202477-3898649884-1000 was added to the local Admin group.
This username is slice1.
2024-07-25 22:03:56.012 +00:00 ‖ DESKTOP-MALD9OV ‖ Sec ‖ 4616 ‖ low ‖ 201 ‖ Unauthorized System Time Modification ‖ PrevTime: 2024-07-25T22:03:56.012867Z ¦ NewTime: 2024-07-25T22:03:56.012000Z ¦ User: WIN-MB9TIUK70HK$ ¦ Proc: C:\Windows\System32\rundll32.exe ¦ PID: 0x4a0 ¦ LID: 0x3e7
2024-07-25 22:03:56.016 +00:00 ‖ DESKTOP-MALD9OV ‖ Sec ‖ 4728 ‖ low ‖ 202 ‖ A Member Was Added to a Security-Enabled Global Group ‖ SrcSID: S-1-5-21-2883796447-3563202477-3898649884-1000 ¦ TgtGrp: None ¦ LID: 0x3e7
2024-07-25 22:03:56.020 +00:00 ‖ DESKTOP-MALD9OV ‖ Sec ‖ 4720 ‖ low ‖ 203 ‖ Local User Account Created ‖ TgtUser: slice1 ¦ TgtSID: S-1-5-21-2883796447-3563202477-3898649884-1000
2024-07-25 22:03:56.049 +00:00 ‖ DESKTOP-MALD9OV ‖ Sec ‖ 4732 ‖ high ‖ 212 ‖ User Added To Local Admin Grp ‖ SrcSID: S-1-5-21-2883796447-3563202477-3898649884-1000 ¦ TgtGrp: Administrators ¦ LID: 0x3e7
2024-07-25 22:05:18.412 +00:00 ‖ DESKTOP-MALD9OV ‖ Sec ‖ 4648 ‖ info ‖ 414 ‖ Explicit Logon ‖ TgtUser: slice1 ¦ SrcUser: WIN-MB9TIUK70HK$ ¦ SrcIP: 127.0.0.1 ¦ Proc: C:\Windows\System32\svchost.exe ¦ TgtSvr: localhost
2024-07-25 22:05:18.412 +00:00 ‖ DESKTOP-MALD9OV ‖ Sec ‖ 4624 ‖ info ‖ 415 ‖ Logon (Interactive) *Creds in memory* ‖ Type: 2 ¦ TgtUser: slice1 ¦ SrcComp: WIN-MB9TIUK70HK ¦ SrcIP: 127.0.0.1 ¦ LID: 0xb6b25
2024-07-25 22:05:18.412 +00:00 ‖ DESKTOP-MALD9OV ‖ Sec ‖ 4624 ‖ info ‖ 416 ‖ Logon (Interactive) *Creds in memory* ‖ Type: 2 ¦ TgtUser: slice1 ¦ SrcComp: WIN-MB9TIUK70HK ¦ SrcIP: 127.0.0.1 ¦ LID: 0xb6b55
2024-07-25 22:05:18.412 +00:00 ‖ DESKTOP-MALD9OV ‖ Sec ‖ 4672 ‖ info ‖ 417 ‖ Admin Logon ‖ TgtUser: slice1 ¦ LID: 0xb6b25
2024-07-25 22:05:19.785 +00:00 ‖ DESKTOP-MALD9OV ‖ Sec ‖ 5379 ‖ low ‖ 427 ‖ Credential Manager Accessed ‖ PID: 1484 ¦ SrcUser: slice1 ¦ Tgt: MicrosoftAccount:user=02yzspbvdvzrqxqh ¦ CredsReturned: 1 ¦ ReturnCode: 3221226021 ¦ LID: 0xb6b55 ¦ SrcSID: S-1-5-21-2883796447-3563202477-3898649884-1000Looking at the computer-name column, you can see that the name was changed several times.
After that, a computer account named LEMON-SQUEEZER$ starts showing suspicious activity, so it looks like the attack began around the time of this rename.
The password policy was changed, and Max. Password Age was set to 83.
Defender was also disabled.
At the end, a user named notabackdoor was also added, and it seems to have been added to the local Admin group.
2024-07-25 22:31:26.470 +00:00 ‖ lemon-squeezer ‖ Sec ‖ 4728 ‖ low ‖ 4857 ‖ A Member Was Added to a Security-Enabled Global Group ‖ SrcSID: S-1-5-21-2883796447-3563202477-3898649884-1001 ¦ TgtGrp: None ¦ LID: 0x44e1d
2024-07-25 22:31:26.472 +00:00 ‖ lemon-squeezer ‖ Sec ‖ 4720 ‖ low ‖ 4858 ‖ Local User Account Created ‖ TgtUser: notabackdoor ¦ TgtSID: S-1-5-21-2883796447-3563202477-3898649884-1001
2024-07-25 22:31:26.570 +00:00 ‖ lemon-squeezer ‖ Sec ‖ 4732 ‖ high ‖ 4871 ‖ User Added To Local Admin Grp ‖ SrcSID: S-1-5-21-2883796447-3563202477-3898649884-1001 ¦ TgtGrp: Administrators ¦ LID: 0x44e1dSummary
I really enjoy this kind of log-analysis forensic challenge.