This page has been machine-translated from the original page.
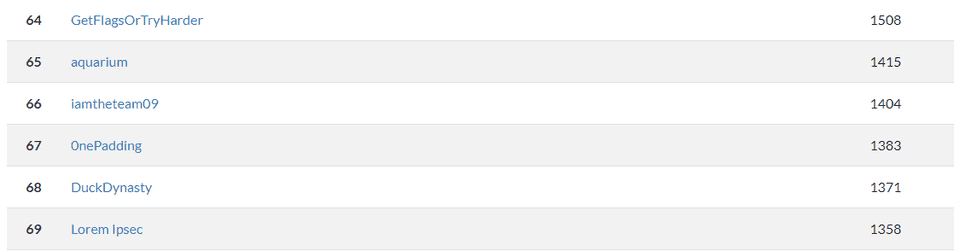
I participated in TUCTF, which was held around December 2, 2023, as part of 0nePadding.
I’ll briefly write up the solutions.
Table of Contents
- What Are You Doing In My Swamp?(Forensic)
- State of the Git(Forensic)
- Table Encryption(Crypto)
- Custom ECB Cipher(Crypto)
- Summary
What Are You Doing In My Swamp?(Forensic)
This challenge is like ogres, it has layers
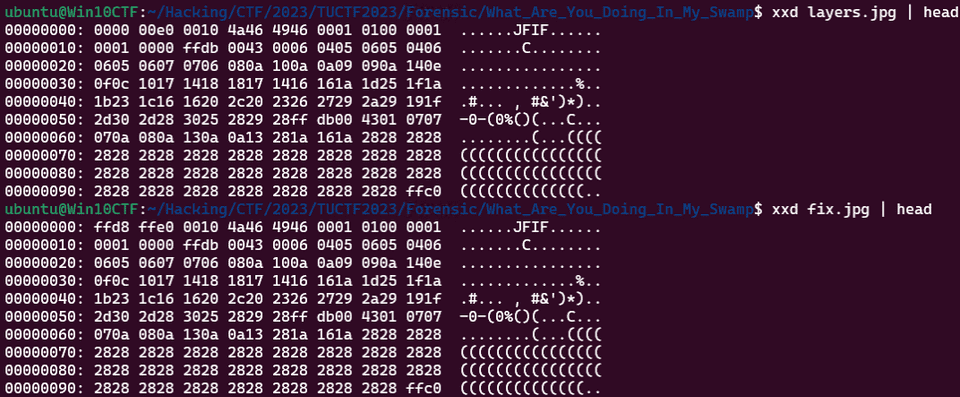
The file provided as the challenge binary had its magic number stripped, so it could not be recognized as an image file. I manually added the JPG magic number.
As a result, I was able to view the following image.
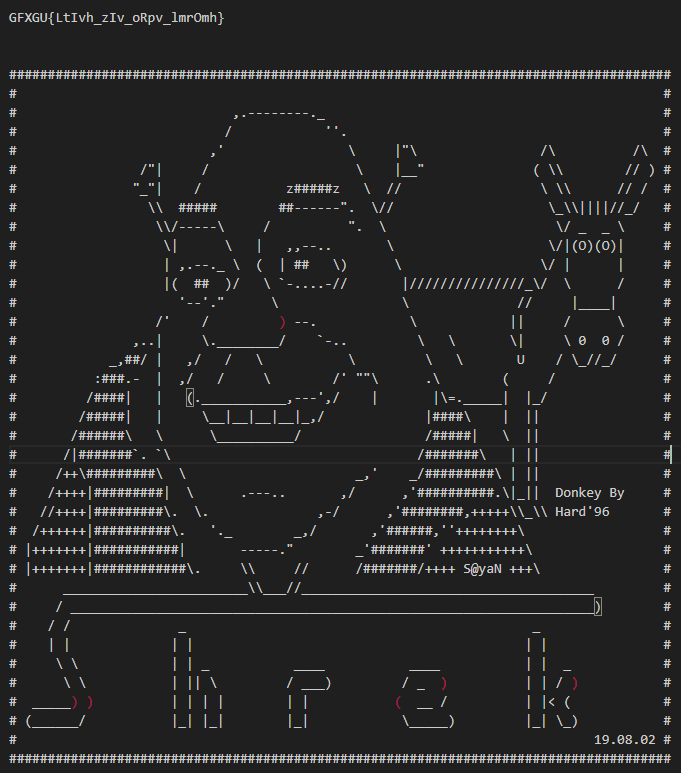
There were no hints from there, so I was stuck for a bit, but in the end I used steghide with the password layers and obtained the following message.
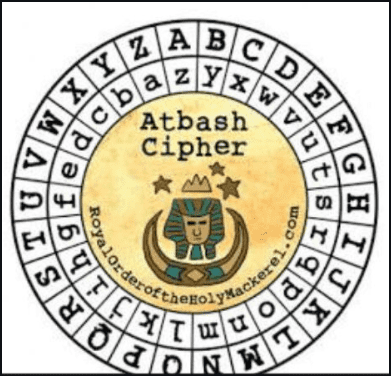
After that, applying an Atbash cipher to GFXGU{LtIvh_zIv_oRpv_lmrOmh} gave me the correct flag.
State of the Git(Forensic)
All the cool kids are embracing state of the art IAC technology, and we are rushing to catch up! We have a new system that we are testing out, but we are not sure how secure it is. Can you check it out for us?
The challenge binary was an archive containing a .git directory and some code.
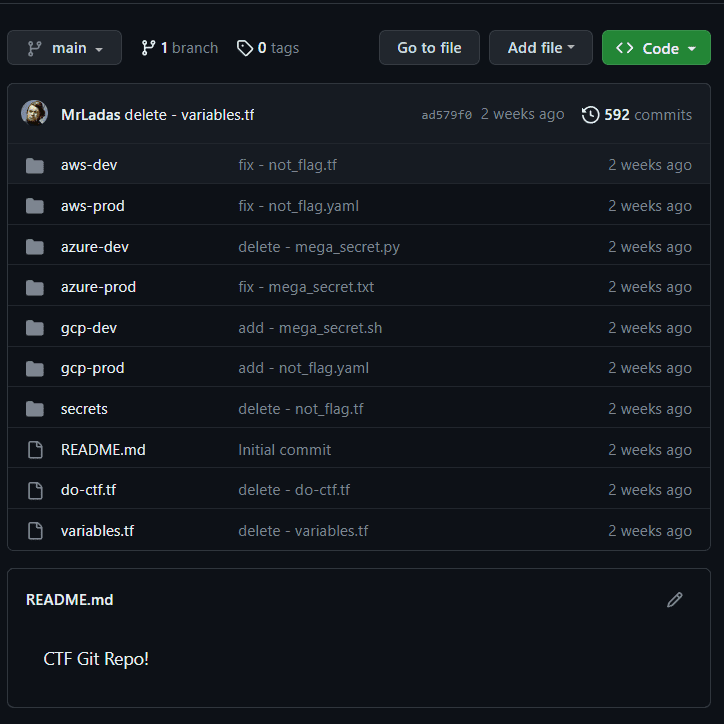
When I tried pushing the provided repository to GitHub, I found that it had as many as 592 commits.
Most of the commit messages start with words like delete, add, release, or fix.
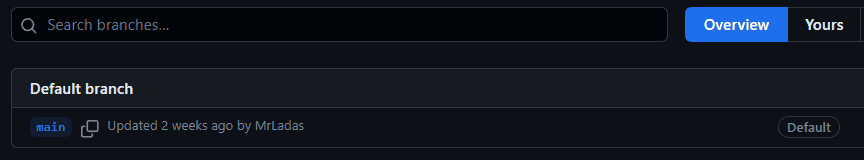
On GitHub, only one branch showed up.
This was entirely my own mistake, but I had only pushed the main branch from the local repository to GitHub, so no matter how much I inspected the code on GitHub, I could not find the flag.
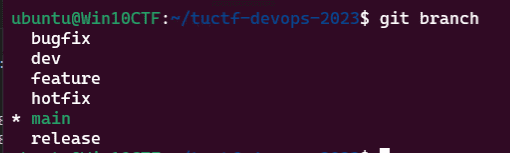
When I checked the local branches, I found that several branches existed.
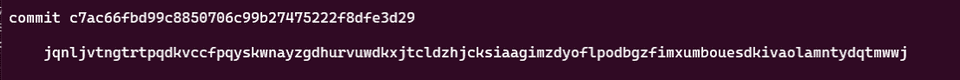
After switching the local branch to release and grepping git log, I found exactly one suspicious commit message.
Investigating this commit revealed that a Base64-encoded flag had been embedded in password.
$ git --no-pager show c7ac66f
commit c7ac66fbd99c8850706c99b27475222f8dfe3d29
Author: MrLadas <97653268+MrLadas@users.noreply.github.com>
Date: Tue Nov 21 23:28:37 2023 +0000
jqnljvtngtrtpqdkvccfpqyskwnayzgdhurvuwdkxjtcldzhjcksiaagimzdyoflpodbgzfimxumbouesdkivaolamntydqtmwwj
diff --git a/terraform.tfstate b/terraform.tfstate
new file mode 100644
index 0000000..955de90
--- /dev/null
+++ b/terraform.tfstate
@@ -0,0 +1,103 @@
+{
+ "version": 4,
+ "terraform_version": "1.6.4",
+ "serial": 3,
+ "lineage": "0d21a79d-34f7-89e7-57f4-9266570147f4",
+ "outputs": {},
+ "resources": [
+ {
+ "mode": "managed",
+ "type": "droplet",
+ "name": "ctfd-dev-01",
+ "provider": "provider[\"registry.terraform.io/digitalocean/digitalocean\"]",
+ "instances": [
+ {
+ "schema_version": 0,
+ "attributes": {
+ "arch": "amd64",
+ "bwlimit": 0,
+ "clone": null,
+ "clone_storage": null,
+ "cmode": "tty",
+ "console": true,
+ "cores": 1,
+ "cpulimit": 0,
+ "cpuunits": 1024,
+ "description": "",
+ "features": [],
+ "force": false,
+ "full": null,
+ "hagroup": "",
+ "hastate": "",
+ "hookscript": "",
+ "hostname": "ctfd-dev-01",
+ "id": "aws/ctfd-dev-01",
+ "ignore_unpack_errors": false,
+ "lock": "",
+ "memory": 512,
+ "mountpoint": [],
+ "nameserver": "",
+ "network": [
+ {
+ "bridge": "vmbr0",
+ "firewall": true,
+ "gw": "192.168.1.1",
+ "gw6": "",
+ "hwaddr": "BC:24:11:15:79:0A",
+ "ip": "192.168.5.250/16",
+ "ip6": "",
+ "mtu": 0,
+ "name": "eth0",
+ "rate": 0,
+ "tag": 0,
+ "trunks": "",
+ "type": "veth"
+ }
+ ],
+ "onboot": true,
+ "ostemplate": "",
+ "ostype": "ubuntu",
+ "password": "VFVDVEZ7NzNycjRmMHJtX1M3QTczLTF5XzUzY3IzNzV9Cg==", // ZG9wX3YxXzA3ZmJjODgwY2YwNTNhOTE5Nzk4MDdkZmFhZjhhZDVjOTg4MGFiYWUxZjhkZjJjY2VjZTk2Njk0MmFmNDE0MDgK < Change this before going !
+ "pool": "Production",
+ "protection": false,
+ "restore": false,
+ "rootfs": [
+ {
+ "acl": false,
+ "quota": false,
+ "replicate": false,
+ "ro": false,
+ "shared": false,
+ "size": "8G",
+ "storage": "do-block-storage",
+ "volume": "do-block-storage:ctfd-dev-01/rootfs"
+ }
+ ],
+ "searchdomain": "",
+ "ssh_public_keys": null,
+ "start": true,
+ "startup": "",
+ "swap": 512,
+ "tags": "",
+ "template": false,
+ "timeouts": null,
+ "tty": 2,
+ "unique": false,
+ "unprivileged": true,
+ "unused": []
+ },
+ "sensitive_attributes": [
+ [
+ {
+ "type": "get_attr",
+ "value": "password"
+ }
+ ]
+ ],
+ "private": "sdkawewgfjfakqpwoqpretwenfwejweahwhuqhewdfhewf"
+ }
+ ]
+ }
+ ],
+ "check_results": null
+}Decoding it gives the flag.
$ echo VFVDVEZ7NzNycjRmMHJtX1M3QTczLTF5XzUzY3IzNzV9Cg== | base64 -d
TUCTF{73rr4f0rm_S7A73-1y_53cr375}Table Encryption(Crypto)
You can’t crack my file! I am the exclusive owner of the encryption key!
The challenge binary was an encrypted binary file named table_encryption.xml.enc.
There were no hints besides the filename, so I started by XORing it with the XML prologue, which allowed me to recover the original key.