This page has been machine-translated from the original page.
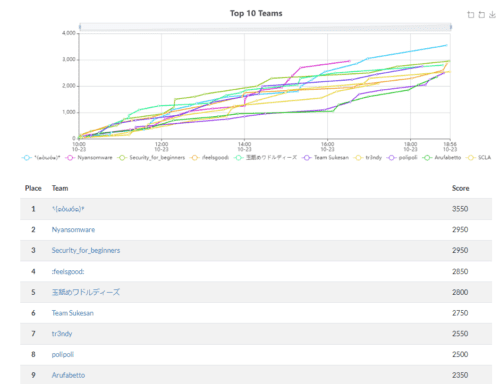
I participated in xINT CTF 2021, held at AVTOKYO 2021 on October 23, 2021!
I ended up in 7th place with 2550 points, which was unfortunately not good enough to reach the top tier, but I had a great time solving problems with two friends as a team for the first time in a while.
From the problems I tackled, I wrote up the ones that were interesting and solved, as well as the ones I was frustrated not to solve.
Table of Contents
Solved
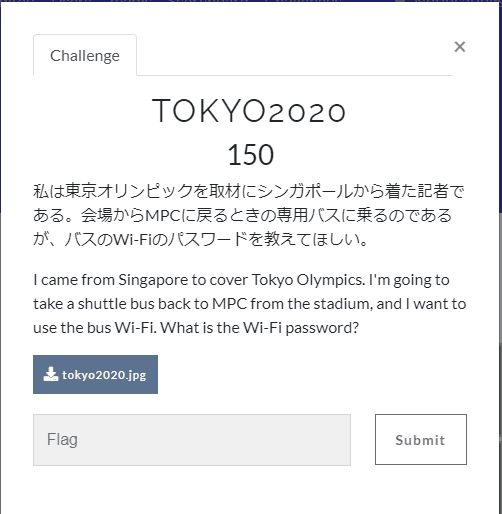
TOKYO2020 (150)
This was the first BUS challenge.
The downloaded image looked like this:
Searching for “MPC bus” revealed that a bus for media personnel was operating during the event.
Tokyo 2020: Establishment of Media Personnel Bus Boarding/Alighting Points
Searching Google and Twitter for leaked Wi-Fi passwords for this media bus revealed that a Korean media outlet called “GO! Tokyo” had leaked an image along with the password, so I found that article and obtained the Flag.
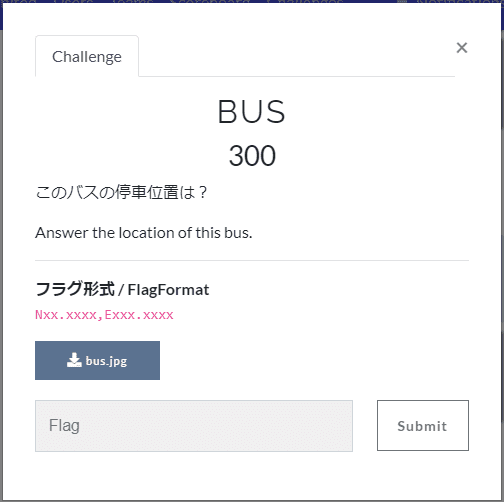
BUS (300)
The second BUS challenge.
Downloading the image yielded this:
From the vehicle number H657-16418, I identified the bus as the Saku/Komoro Express (Takamine Kogen/Komoro/Saku – Shinjuku Line).
Reference: JR Bus Kanto Komoro Branch - Wikipedia
Next, I extracted the shooting time from the EXIF data of the downloaded image, compared it with the timetable for the above bus line, and identified the stop as Sakudaira Station.
A car rental shop was reflected in the window of the image, so I searched Google Maps for the bus stop across from the car rental shop to GET the Flag.
soar to new heights (300)
The third BUS challenge.
Here is the downloadable image:
Carefully reading the sign in the direction the bus is traveling reveals Cold Spring Valley.
Searching for schools in Cold Spring Valley turned up a school officially named Michael Inskeep Elementary School that was scheduled to open in Cold Springs in the summer of 2021.
Reference: Building / School Naming
Searching by this person’s name led to the following page, where the alt text of an embedded image revealed his wife’s name:
Reference: Inskeep Elementary / Namesake: Michael Inskeep
Unsolved
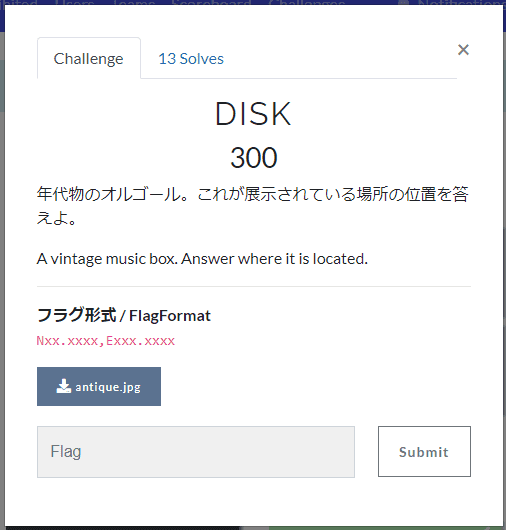
DISK
Here is the problem:
And the downloaded image:
Googling the corporate motto visible in the background of this image reveals that it belongs to Pioneer Corporation.
The image shows a statue and a music box, so I searched for things like “Pioneer statue” and “Pioneer music box.”
A search for “Pioneer statue” returned this blog near the top.
It turns out the image shows Pioneer’s Kawagoe plant main entrance.
However, entering the coordinates of the Kawagoe plant from Google Maps did not lead to the correct answer.
Solution
According to the Open xINT CTF 2021 write-up, the EXIF data of the image on the blog above contained location information, and the correct answer was a point slightly offset from it. (Who could possibly solve that…?)
That said, what I genuinely felt I lacked was the immediate awareness that resized images have their EXIF data rewritten.
The image in the article was served in a resized form like [h]ttps://xxxxx/xxx/img_7433.jpg?w=460&h=345, so I needed to download the original unresized image at [h]ttps://xxxxx/xxx/img_7433.jpg to extract location data from the EXIF.
In hindsight it is obvious, but going forward I need to remember to obtain the original image before reading EXIF data.
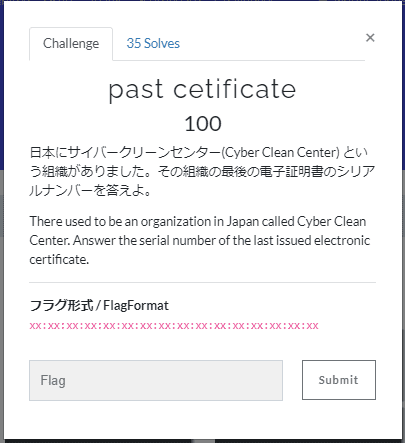
past certificate
Here is the challenge.
The task was to identify the serial number of the last certificate for a domain that had already been closed (ccc.go.jp).
I searched around OCSP-related data since the certificate seemed to be expired, but could not find useful information and gave up.
Solution
It turns out this was a problem about understanding Certificate Transparency (CT), a mechanism for certificate issuance and monitoring.
Reference: Let’s learn about Certificate Transparency
Certificate Transparency is defined in RFC 6962; it is a system for recording all certificates issued by certificate authorities as open-source logs so that incorrect or malicious certificates can be monitored by everyone.
Certificate logs are recorded on public servers called CT log servers.
If a certificate supports CT, the CT log server returns a valid SCT (Signed Certificate Timestamp).
CT log servers exist around the world; well-known ones include Google’s servers as well as those from DigiCert and Symantec.
You can search CT server logs at sites like crt.sh. In this problem, searching for the certificate through this site would have led to the Flag. Interesting.
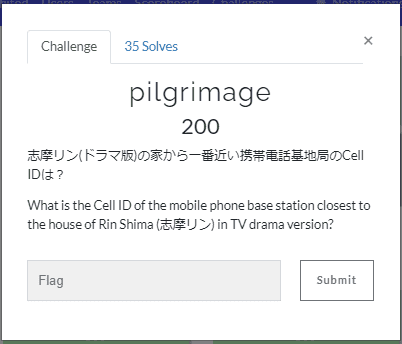
pilgrimage
The challenge was as follows:
I quickly found the address of the house from the TV drama by Googling, but I could not figure out how to identify the Cell ID of the nearby base station, so I gave up.
I was so stuck that I seriously considered driving out to Yamanashi to check in person (laughs).
Solution
Looking at writeups, it turned out the answer could be found using OpenCelliD, an open-source cellular base station database.
Reference: Open xINT CTF 2021 write-up
I wonder why I didn’t find this site despite searching for so long…
Summary
OSINT CTFs are not something I usually tackle, so it was a refreshing and very enjoyable experience.
It reminded me how fun it is to participate as a team, so I would like to team up with someone more often for CTFs going forward.
In any case, many thanks to the AVTOKYO organizers and the team members who participated with me!